Nmap Scanning - whiteowl911/leveleffect GitHub Wiki
What is Nmap and How to Use it – A Tutorial for the Greatest Scanning Tool of All Time
Nmap is the most famous scanning tool used by penetration testers. In this article, we will look at some core features of Nmap along with a few useful commands.
What is Nmap?
Nmap is short for Network Mapper. It is an open-source Linux command-line tool that is used to scan IP addresses and ports in a network and to detect installed applications.
Nmap allows network admins to find which devices are running on their network, discover open ports and services, and detect vulnerabilities.
Gordon Lyon (pseudonym Fyodor) wrote Nmap as a tool to help map an entire network easily and to find its open ports and services.
Nmap has become hugely popular, being featured in movies like The Matrix and the popular series Mr. Robot.
Why use Nmap?
There are a number of reasons why security pros prefer Nmap over other scanning tools.
First, Nmap helps you to quickly map out a network without sophisticated commands or configurations. It also supports simple commands (for example, to check if a host is up) and complex scripting through the Nmap scripting engine.
Other features of Nmap include:
- Ability to quickly recognize all the devices including servers, routers, switches, mobile devices, etc on single or multiple networks.
- Helps identify services running on a system including web servers, DNS servers, and other common applications. Nmap can also detect application versions with reasonable accuracy to help detect existing vulnerabilities.
- Nmap can find information about the operating system running on devices. It can provide detailed information like OS versions, making it easier to plan additional approaches during penetration testing.
- During security auditing and vulnerability scanning, you can use Nmap to attack systems using existing scripts from the Nmap Scripting Engine.
- Nmap has a graphical user interface called Zenmap. It helps you develop visual mappings of a network for better usability and reporting.
Commands
Let's look at some Nmap commands. If you don't have Nmap installed, you can get it from here.
Basic scans
Scanning the list of active devices on a network is the first step in network mapping. There are two types of scans you can use for that:
- Ping scan — Scans the list of devices up and running on a given subnet.
> nmap -sp 192.168.1.1/24
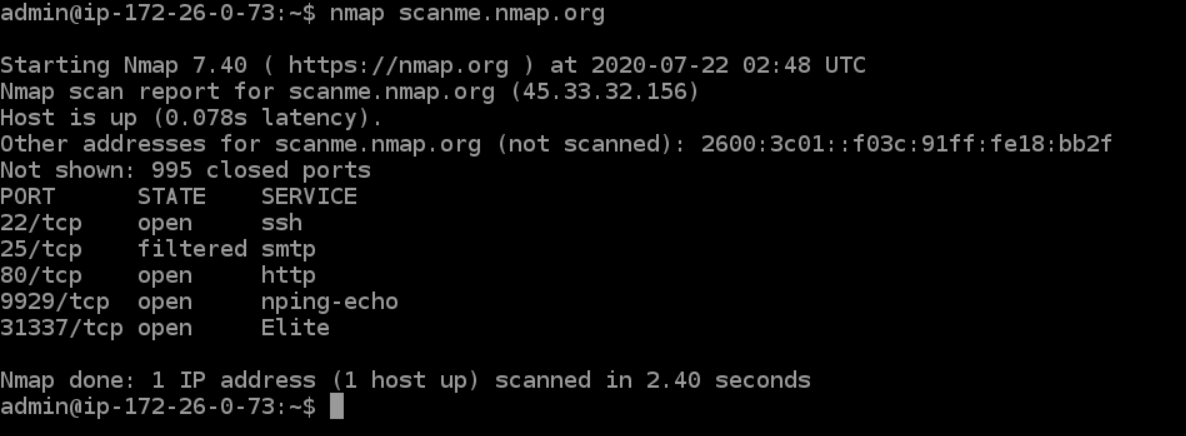
- Scan a single host — Scans a single host for 1000 well-known ports. These ports are the ones used by popular services like SQL, SNTP, apache, and others.
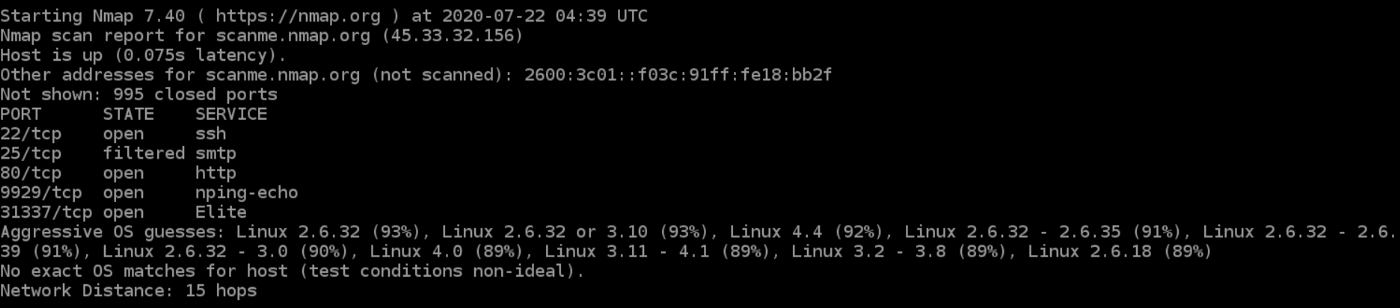
> nmap scanme.nmap.org
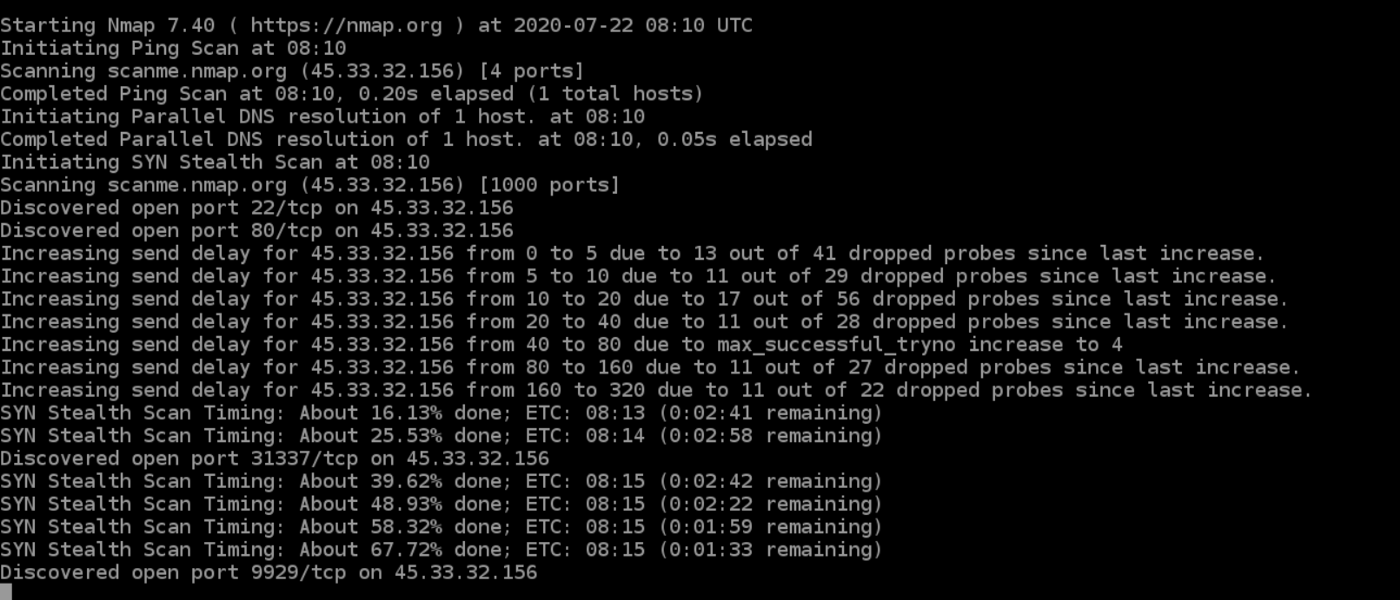
Stealth scan
Stealth scanning is performed by sending an SYN packet and analyzing the response. If SYN/ACK is received, it means the port is open, and you can open a TCP connection.
However, a stealth scan never completes the 3-way handshake, which makes it hard for the target to determine the scanning system.
> nmap -sS scanme.nmap.org
You can use the ‘-sS’ command to perform a stealth scan. Remember, stealth scanning is slower and not as aggressive as the other types of scanning, so you might have to wait a while to get a response.
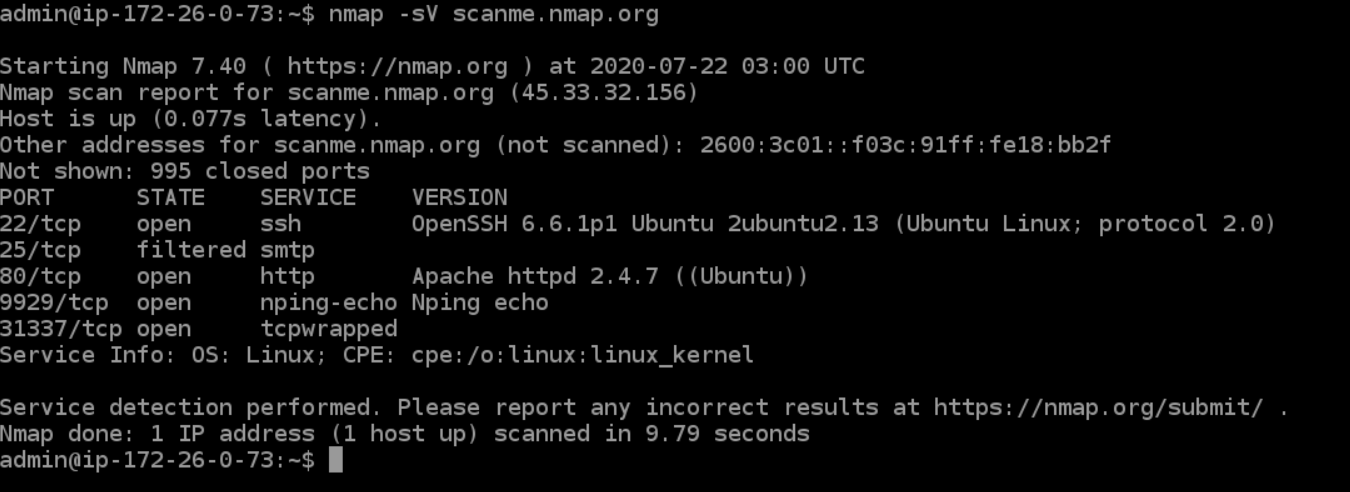
Version scanning
Finding application versions is a crucial part in penetration testing.
It makes your life easier since you can find an existing vulnerability from the Common Vulnerabilities and Exploits (CVE) database for a particular version of the service. You can then use it to attack a machine using an exploitation tool like Metasploit.
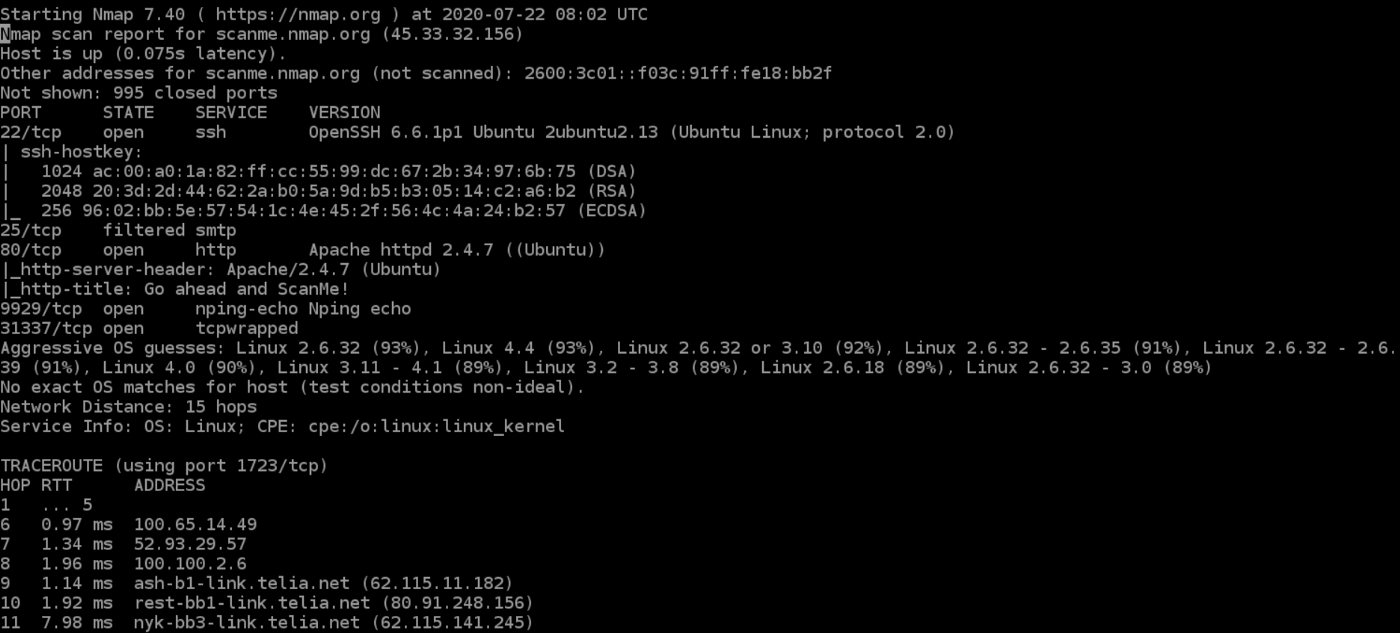
> nmap -sV scanme.nmap.org
To do a version scan, use the ‘-sV’ command. Nmap will provide a list of services with its versions. Do keep in mind that version scans are not always 100% accurate, but it does take you one step closer to successfully getting into a system.
OS Scanning
In addition to the services and their versions, Nmap can provide information about the underlying operating system using TCP/IP fingerprinting. Nmap will also try to find the system uptime during an OS scan.
> nmap -sV scanme.nmap.org
You can use the additional flags like osscan-limit to limit the search to a few expected targets. Nmap will display the confidence percentage for each OS guess.
Again, OS detection is not always accurate, but it goes a long way towards helping a pen tester get closer to their target.
Aggressive Scanning
Nmap has an aggressive mode that enables OS detection, version detection, script scanning, and traceroute. You can use the -A argument to perform an aggressive scan.
> nmap -A scanme.nmap.org
Aggressive scans provide far better information than regular scans. However, an aggressive scan also sends out more probes, and it is more likely to be detected during security audits.
Scanning Multiple Hosts
Nmap has the capability of scanning multiple hosts simultaneously. This feature comes in real handy when you are managing vast network infrastructure.
You can scan multiple hosts through numerous approaches:
- Write all the IP addresses in a single row to scan all of the hosts at the same time.
> nmap 192.164.1.1 192.164.0.2 192.164.0.2
- Use the asterisk (*) to scan all of the subnets at once.
> nmap 192.164.1.*
- Add commas to separate the addresses endings instead of typing the entire domains.
> nmap 192.164.0.1,2,3,4
- Use a hyphen to specify a range of IP addresses
> nmap 192.164.0.0–255
Port Scanning
Port scanning is one of the most fundamental features of Nmap. You can scan for ports in several ways.
- Using the -p param to scan for a single port
> nmap -p 973 192.164.0.1
- If you specify the type of port, you can scan for information about a particular type of connection, for example for a TCP connection.
> nmap -p T:7777, 973 192.164.0.1
- A range of ports can be scanned by separating them with a hyphen.
> nmap -p 76–973 192.164.0.1
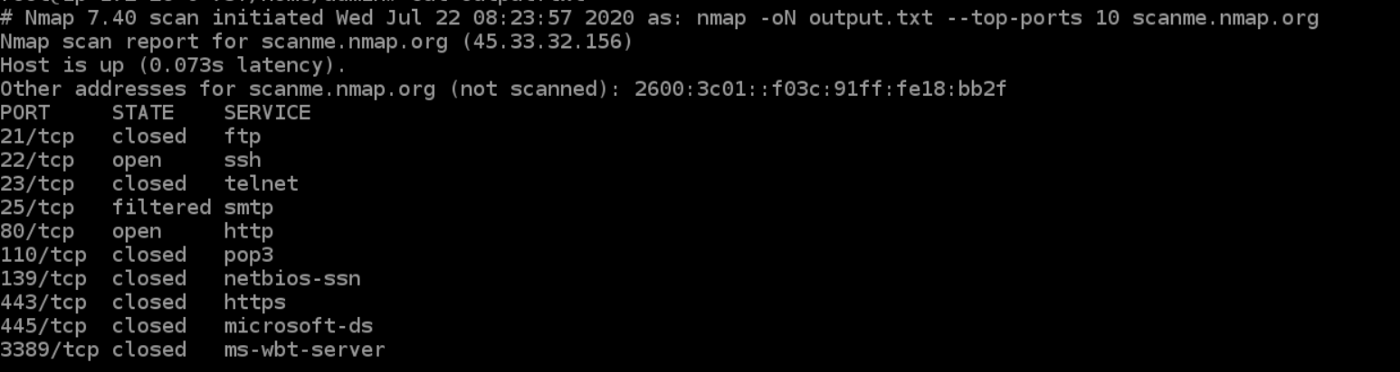
- You can also use the -top-ports flag to specify the top n ports to scan.
> nmap --top-ports 10 scanme.nmap.org
Scanning from a File
If you want to scan a large list of IP addresses, you can do it by importing a file with the list of IP addresses.
> nmap -iL /input_ips.txt
The above command will produce the scan results of all the given domains in the “input_ips.txt” file. Other than simply scanning the IP addresses, you can use additional options and flags as well.
Verbosity and Exporting Scan Results
Penetration testing can last days or even weeks. Exporting Nmap results can be useful to avoid redundant work and to help with creating final reports. Let’s look at some ways to export Nmap scan results.
Verbose Output
> nmap -v scanme.nmap.org
The verbose output provides additional information about the scan being performed. It is useful to monitor step by step actions Nmap performs on a network, especially if you are an outsider scanning a client’s network.
Normal output
Nmap scans can also be exported to a text file. It will be slightly different from the original command line output, but it will capture all the essential scan results.
> nmap -oN output.txt scanme.nmap.org
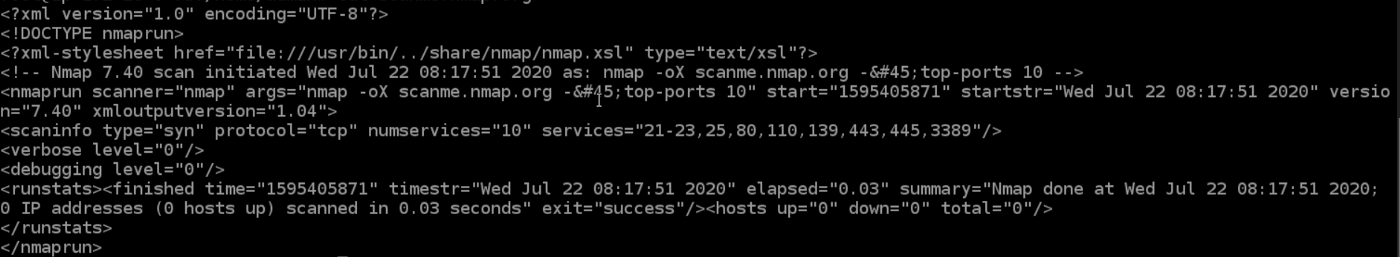
XML output
Nmap scans can also be exported to XML. It is also the preferred file format of most pen-testing tools, making it easily parsable when importing scan results.
> nmap -oX output.xml scanme.nmap.org
Multiple Formats
You can also export the scan results in all the available formats at once using the -oA command.
> nmap -oA output scanme.nmap.org
The above command will export the scan result in three files — output.xml, output. Nmap and output.gnmap.
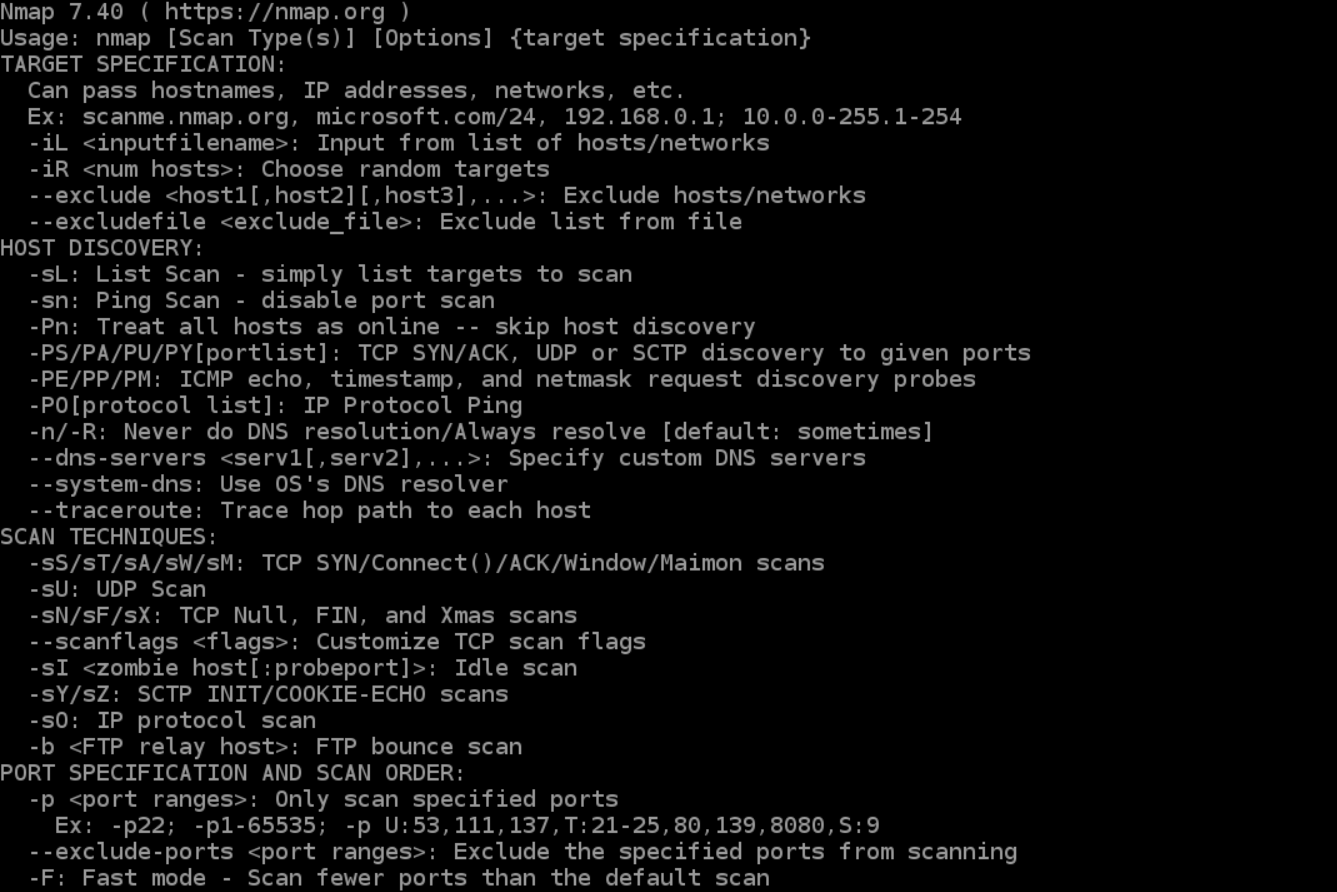
Nmap Help
Nmap has a built-in help command that lists all the flags and options you can use. It is often handy given the number of command-line arguments Nmap comes with.
> nmap -h
Nmap Scripting Engine
Nmap Scripting Engine (NSE) is an incredibly powerful tool that you can use to write scripts and automate numerous networking features.
You can find plenty of scripts distributed across Nmap, or write your own script based on your requirements. You can even modify existing scripts using the Lua programming language.
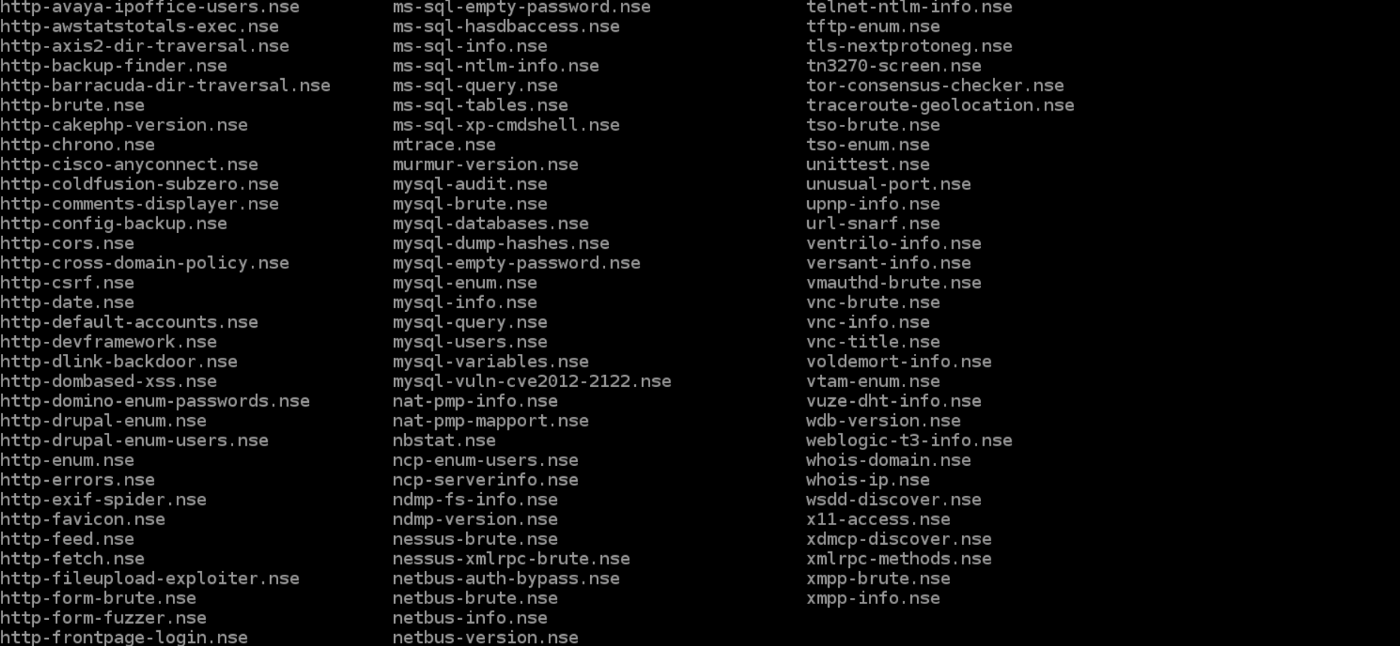
NSE also has attack scripts that are used in attacking the network and various networking protocols.
Going through the scripting engine in-depth would be out-of-scope for this article, so here is more information about the Nmap scripting engine.
Zenmap
Zenmap is a graphical user interface for Nmap. It is a free and open-source software that helps you get up and running with Nmap.
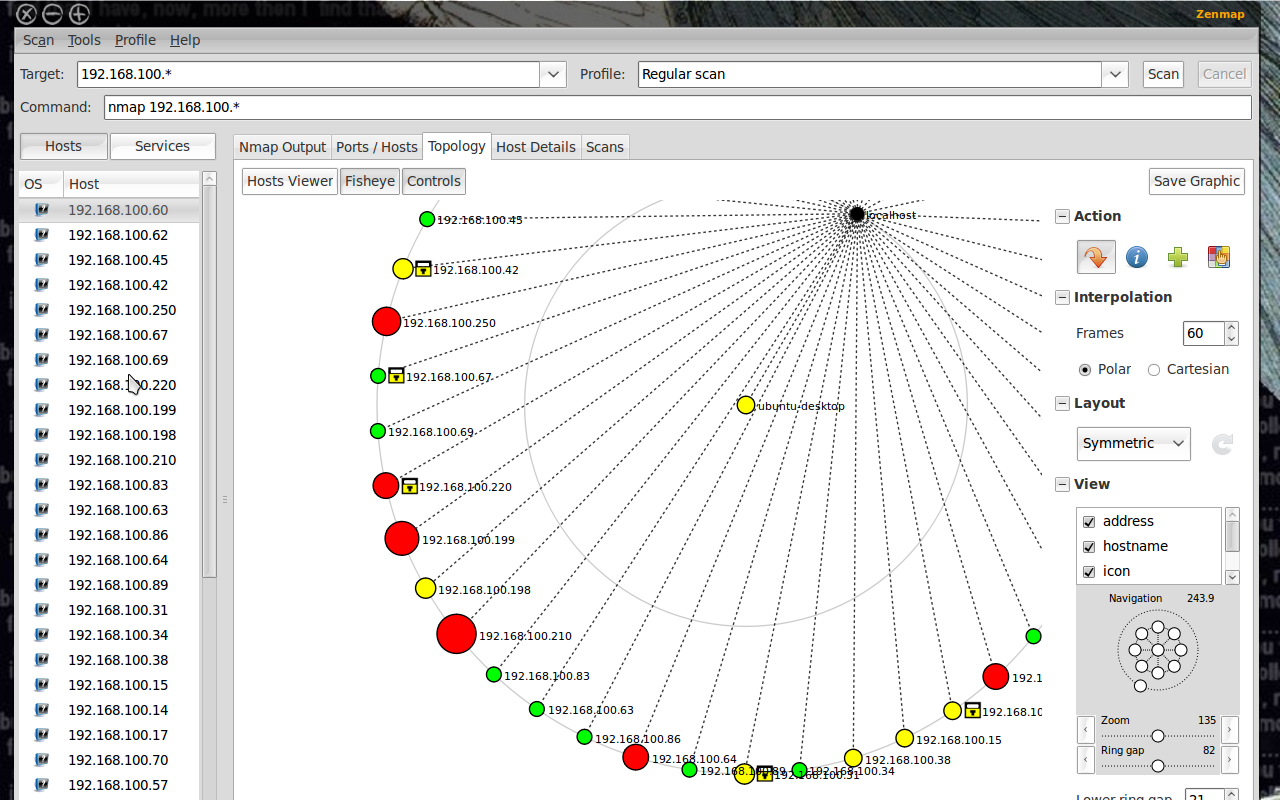
In addition to providing visual network mappings, Zenmap also allows you to save and search your scans for future use.
Zenmap is great for beginners who want to test the capabilities of Nmap without going through a command-line interface.
Conclusion
Nmap is clearly the “Swiss Army Knife” of networking, thanks to its inventory of versatile commands.
It lets you quickly scan and discover essential information about your network, hosts, ports, firewalls, and operating systems.
Nmap has numerous settings, flags, and preferences that help system administrators analyze a network in detail.
If you want to learn Nmap in-depth, here is a great resource for you.
Nmap Cheat Sheet
Nmap has a multitude of options, when you first start playing with this excellent tool, it can be a bit daunting.
In this cheat sheet, you will find a series of practical example commands for running Nmap and getting the most of this powerful tool.
Keep in mind this cheat sheet merely touches the surface of the available options. The Nmap Documentation portal is your reference for digging deeper into the options available.
Nmap Target Selection
Scan a single IP
nmap 192.168.1.1
Scan a host
nmap www.testhostname.com
Scan a range of IPs
nmap 192.168.1.1-20
Scan a subnet
nmap 192.168.1.0/24
Scan targets from a text file
nmap -iL list-of-ips.txt
These are all default scans, which will scan 1000 TCP ports. Host discovery will take place.
Nmap Port Selection
Scan a single Port
nmap -p 22 192.168.1.1
Scan a range of ports
nmap -p 1-100 192.168.1.1
Scan 100 most common ports (Fast)
nmap -F 192.168.1.1
Scan all 65535 ports
nmap -p- 192.168.1.1
Nmap Port Scan types
Scan using TCP connect
nmap -sT 192.168.1.1
Scan using TCP SYN scan (default)
nmap -sS 192.168.1.1
Scan UDP ports
nmap -sU -p 123,161,162 192.168.1.1
Scan selected ports - ignore discovery
nmap -Pn -F 192.168.1.1
Privileged access is required to perform the default SYN scans. If privileges are insufficient a TCP connect scan will be used. A TCP connect requires a full TCP connection to be established and therefore is a slower scan. Ignoring discovery is often required as many firewalls or hosts will not respond to PING, so could be missed unless you select the -Pn parameter. Of course this can make scan times much longer as you could end up sending scan probes to hosts that are not there.
Take a look at the Nmap Tutorial for a detailed look at the scan process.
Service and OS Detection
Detect OS and Services
nmap -A 192.168.1.1
Standard service detection
nmap -sV 192.168.1.1
More aggressive Service Detection
nmap -sV --version-intensity 5 192.168.1.1
Lighter banner grabbing detection
nmap -sV --version-intensity 0 192.168.1.1
Service and OS detection rely on different methods to determine the operating system or service running on a particular port. The more aggressive service detection is often helpful if there are services running on unusual ports. On the other hand the lighter version of the service will be much faster as it does not really attempt to detect the service simply grabbing the banner of the open service.
Nmap Output Formats
Save default output to file
nmap -oN outputfile.txt 192.168.1.1
Save results as XML
nmap -oX outputfile.xml 192.168.1.1
Save results in a format for grep
nmap -oG outputfile.txt 192.168.1.1
Save in all formats
nmap -oA outputfile 192.168.1.1
The default format could also be saved to a file using a simple file redirect command > file. Using the -oN option allows the results to be saved but also can be monitored in the terminal as the scan is under way.
Nmap Output to CSV
Nmap by default has no csv output format. Use the XML output to extract the relevant fields into csv with python.
Jump over to github and grab our sample script that can be easily modified depending on your requirements. With csv files it is easy to convert into xlsx for reporting. This can be done manually or using our python conversion script.
Digging deeper with NSE Scripts
Scan using default safe scripts
nmap -sV -sC 192.168.1.1
Get help for a script
nmap --script-help=ssl-heartbleed
Scan using a specific NSE script
nmap -sV -p 443 –script=ssl-heartbleed.nse 192.168.1.1
Scan with a set of scripts
nmap -sV --script=smb* 192.168.1.1
According to my Nmap install there are currently 581 NSE scripts. The scripts are able to perform a wide range of security related testing and discovery functions. If you are serious about your network scanning you really should take the time to get familiar with some of them.
The option --script-help=$scriptname will display help for the individual scripts. To get an easy list of the installed scripts try locate nse | grep script.
You will notice I have used the -sV service detection parameter. Generally most NSE scripts will be more effective and you will get better coverage by including service detection.
A scan to search for DDOS reflection UDP services
Scan for UDP DDOS reflectors
nmap –sU –A –PN –n –pU:19,53,123,161 –script=ntp-monlist,dns-recursion,snmp-sysdescr 192.168.1.0/24
UDP based DDOS reflection attacks are a common problem that network defenders come up against. This is a handy Nmap command that will scan a target list for systems with open UDP services that allow these attacks to take place. Full details of the command and the background can be found on the Sans Institute Blog where it was first posted.
HTTP Service Information
Gather page titles from HTTP services
nmap --script=http-title 192.168.1.0/24
Get HTTP headers of web services
nmap --script=http-headers 192.168.1.0/24
Find web apps from known paths
nmap --script=http-enum 192.168.1.0/24
There are many HTTP information gathering scripts, here are a few that are simple but helpful when examining larger networks. Helps in quickly identifying what the HTTP service that is running on the open port. Note the http-enum script is particularly noisy. It is similar to Nikto in that it will attempt to enumerate known paths of web applications and scripts. This will inevitably generated hundreds of 404 HTTP responses in the web server error and access logs.
Detect Heartbleed SSL Vulnerability
Heartbleed Testing
nmap -sV -p 443 --script=ssl-heartbleed 192.168.1.0/24
Heartbleed detection is one of the available SSL scripts. It will detect the presence of the well known Heartbleed vulnerability in SSL services. Specify alternative ports to test SSL on mail and other protocols (Requires Nmap 6.46).
IP Address information
Find Information about IP address
nmap --script=asn-query,whois,ip-geolocation-maxmind 192.168.1.0/24
Gather information related to the IP address and netblock owner of the IP address. Uses ASN, whois and geoip location lookups. See the IP Tools for more information and similar IP address and DNS lookups.
Remote Scanning
Testing your network perimeter from an external perspective is key when you wish to get the most accurate results. By assessing your exposure from the attackers perspective you can validate firewall rule audits and understand exactly what is allowed into your network. This is the reason we offer a hosted or online version of the Nmap port scanner. To enable remote scanning easily and effectively because anyone who has played with shodan.io knows very well how badly people test their perimeter networks.
Additional Resources
The above commands are just a taste of the power of Nmap. Check out our Nmap Tutorial that has more information and tips.
You could also view the full set of features by running Nmap with no options. The creator of Nmap, Fyodor, has a book available that covers the tool in depth.
Know Your Network
Hosted Nmap for external port scanning