07. Request Data Verification - cafe24github/cafe24_app_pg_sample GitHub Wiki
These are request-data verification methods we suggest including in your endpoint handlers to make sure the request your app receives are valid.
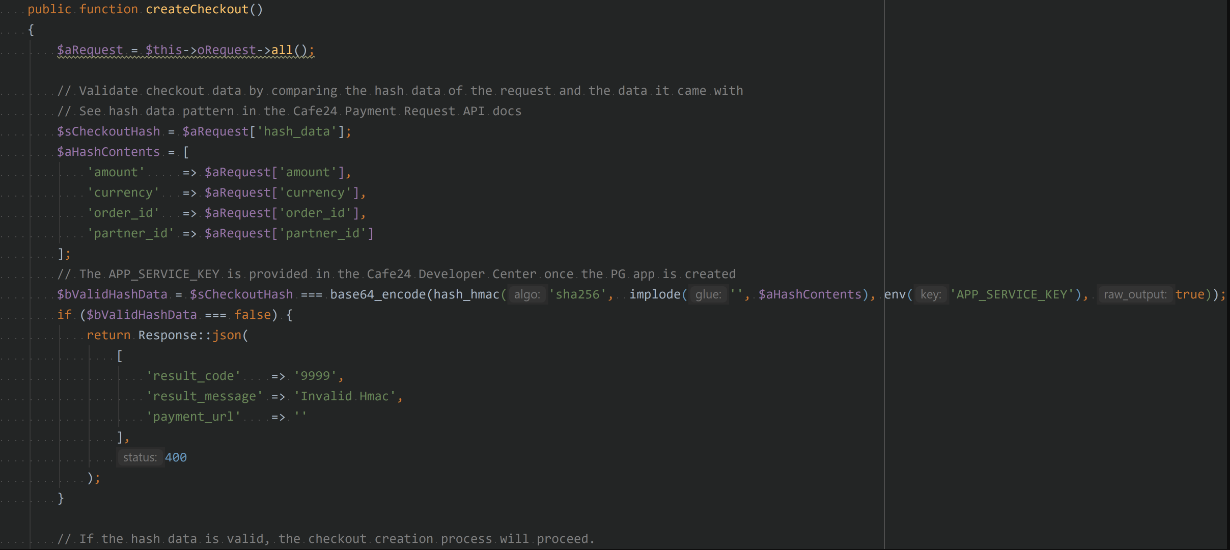
Cafe24 HMAC
Cafe24 uses HMAC validation (hash-based message authentication code) to ensure data integrity in requests they send to the PG app. They are included in the request parameters as hash_data to validate the data they came with.
Format: base64_encode(hash_hmac('sha256', plain text, service_key, true))
Where plain text is the concatenation of the following:
- amount: Total amount paid
- currency: Currency
- order_id: Member store order number
- partner_id: Member store ID
- service_key: Service key issued by the Developers admin when creating the app
Example: base64_encode(hash_hmac('sha256', 'amount+currency+order_id+partner_id', service_key, true))
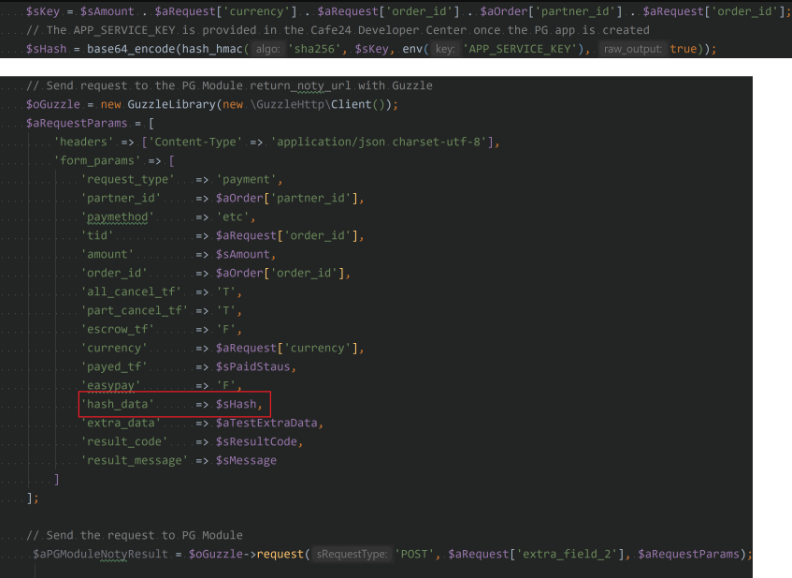
When sending webhook updates (via return_noty_url) to Cafe24, they also require the sender to include HMAC data with the request.
Order Data
To make sure the order data in the callback/webhook request is valid, you can use the PG Company's anti-tampering data. The concept works the same as the Cafe24 HMAC data where you compare the digest from the request and the generated digest in the PG app.
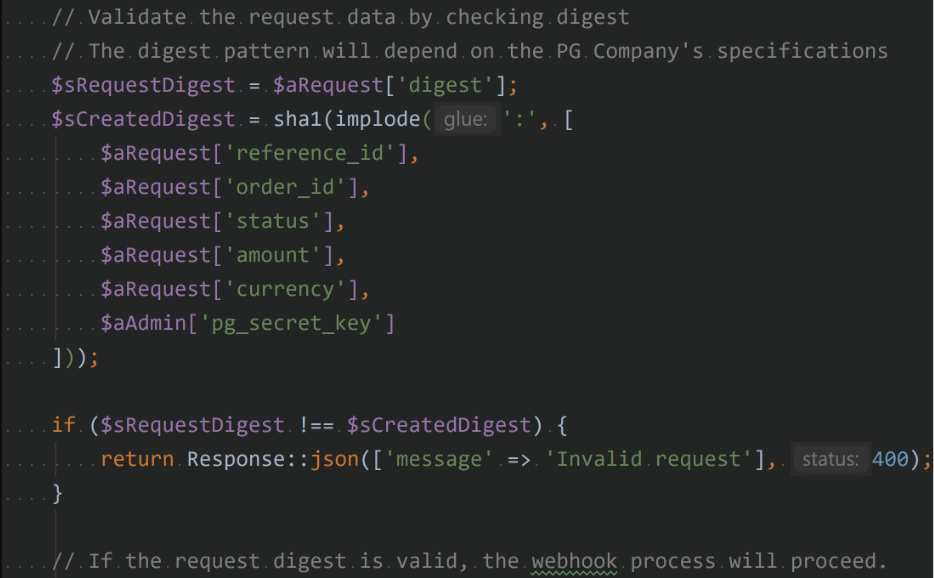
If the PG Company does not provide anti-tampering data, you may use their read order endpoint to know if the order is in their system.
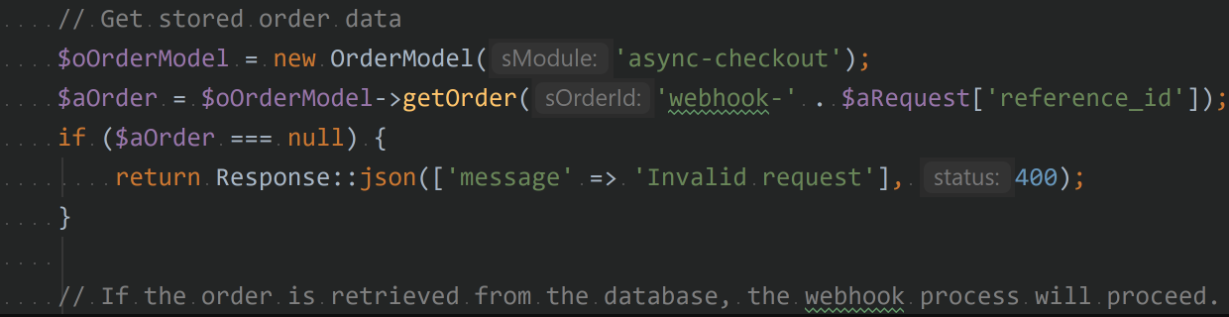
Another way to validate order data is to fetch it from your PG app's database and make sure the important data is valid.