Class 01 - birlzhimself/401-Reading-Notes GitHub Wiki
Strategic Policy Development
To convince a future company to pursue SOC2 compliance, I would highlight the benefits of SOC2 certification. SOC2 certification demonstrates to customers and partners that the company has established strong controls and processes to protect their sensitive data. It also helps the company stand out in a competitive market and can lead to increased trust and credibility among stakeholders. In addition, SOC2 compliance can help mitigate the risk of data breaches and other security incidents, which can have significant financial and reputational consequences.
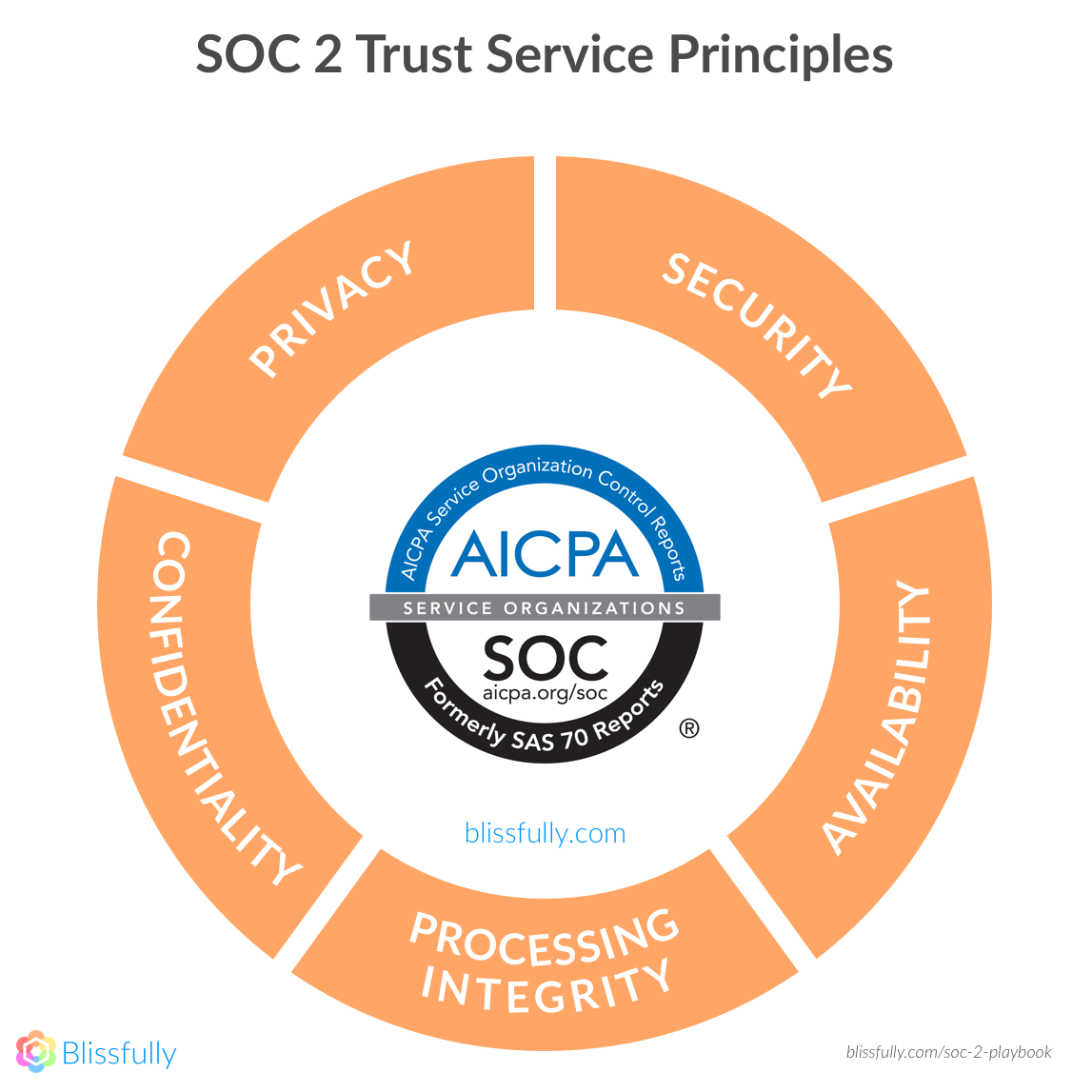
The five SOC2 Trust Principles are:
Security:
The system is protected against unauthorized access, both physical and logical.
Availability:
The system is available for operation and use as agreed upon with customers.
Processing integrity:
System processing is complete, accurate, timely, and authorized.
Confidentiality:
Information designated as confidential is protected as committed or agreed upon with customers.
Privacy:
Personal information is collected, used, retained, disclosed, and disposed of in accordance with the organization's privacy notice and criteria set forth in the Trust Services Criteria.
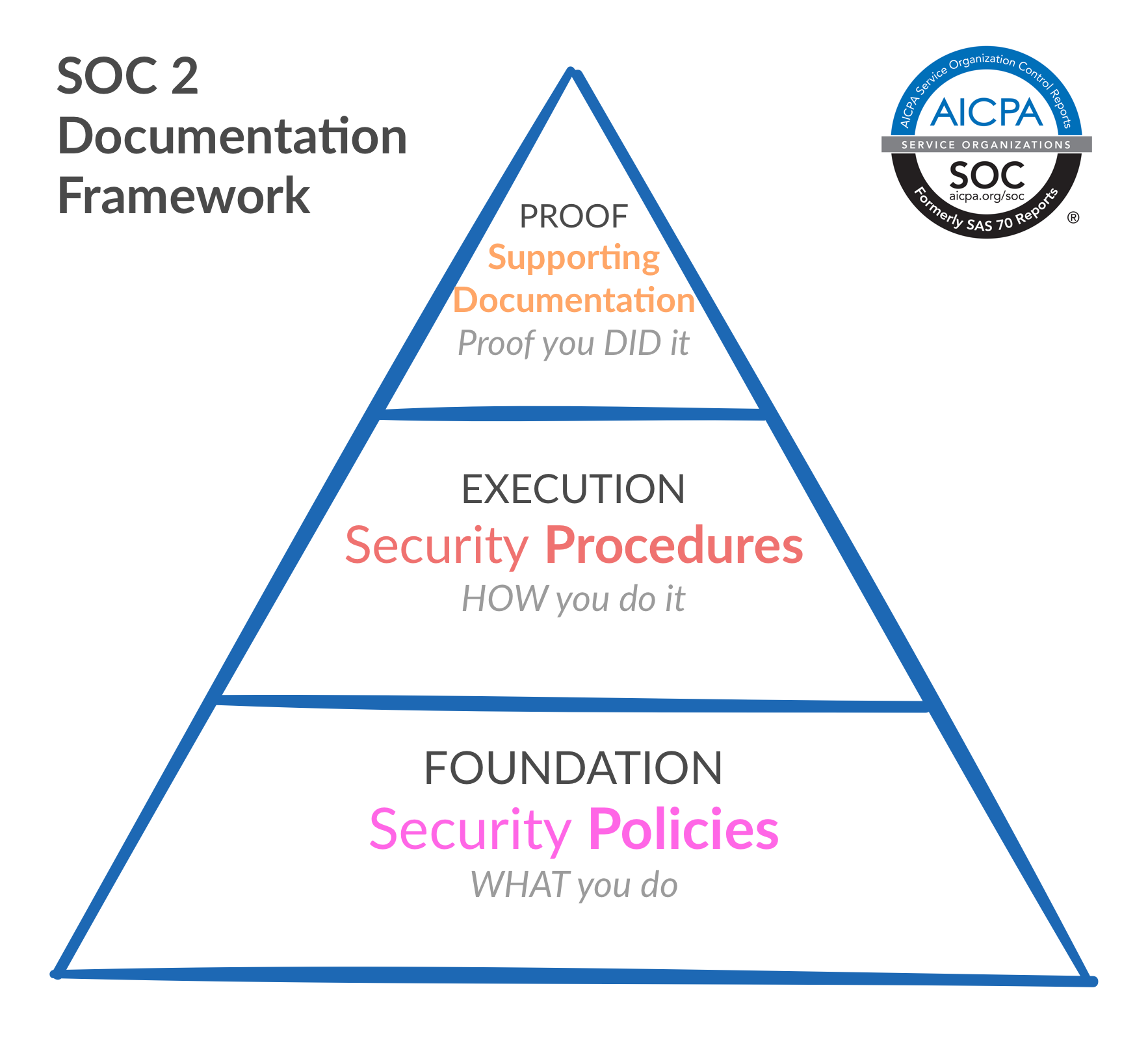
To explain the three levels of the SOC2 pyramid, I would use the following analogy:
Level 1:
The company has built a strong foundation of security controls and processes, similar to the base of a pyramid. These controls provide a solid base for the company to build upon, and help ensure that the company is protected against basic security threats.
Level 2:
As the company grows and becomes more complex, additional controls and processes are needed to protect against more advanced threats. This is similar to the middle section of a pyramid, where additional layers are added to provide additional support and strength.
Level 3:
At the top of the pyramid, the company has achieved the highest level of SOC2 compliance. This means that the company has implemented advanced controls and processes to protect against the most sophisticated threats, and has demonstrated a high level of commitment to security and data protection. This is similar to the top of a pyramid, where the apex is the smallest and most critical point, but also the strongest and most visible.
Links provided:
Reading
The Ultimate Guide to SOC 2 Compliance