10 Class 09: Learning Journal - VascoLucas01/cybersecurity-reading-notes GitHub Wiki
Introduction
[Date: 2023/05/03]
In this Class 09: Learning Journal, I am going to talk about the main ideas/concepts covered in the public key infrasstructure lecture.
Today I Learned
Encoding
- Encoding is the process of putting a sequence of characters into a specialized format
- Decoding is the process of converting an encoded format back into the original sequence of characters
Asymmetric Key Cryptography
Public key cryptography
Public key infrastructure (PKI):
- Certificates
- HTTPS
- Pretty Good Privacy (PGP)
Symmetric Encryption
- Same secret key is used for ecnryption and decryption
- Fast - suitable for bulk encryption of large amount of data
- Problem storing and distributing key securely
- Confidentiality only - sender and recipient know the same key
Symmetric Algorithms
Modern, secure symmetric algorithms:
- AES (Advanced Encryption Standard, also known as Rijndael) is the most popular and widely used symmetric encryption algorithm
Insecure symmetric algorithms:
- DES 56-bit key size, practically broken, can be brute-forced
- 3DES (Triple DES) 64-bit cipher, considered broken
- RC2 64-bit cipher, considered broken
- RC4 stream cipher, broken, practical attacks demonstrated
- Blowfish old 64-bit cipher, broken, practical attacks demonstrated
- GOST Russian 64-bit block cipher, disputable security, considered risky
Asymmetric Encryption
Public/private key pair:
- If the public key encrypts, only the private key can decrypt
- If the private key encrypts, only the public key encrypts
- Private key cannot be derived from the public key
- Private key must be kept secret
- Public key is easy to distribute (anyone can have it)
Message size is limited to key size so not suitable for large.
Used for small amounts of authentication data.
Asymmetric Algorithms
Asymmetric key cryptosystems provide:
- Key-pair generation
- Encryption algorithms
- Digital signature algorithms
- Key exchange algorithms
In public key cryptosystems, a message encrypted by the public key is later decrypted by the private key.
Public Key Cryptography Algorithms
RSA algorithm (Rivest, Shamir, Adleman)
- Basis of many public key cryptography schemes
- Trapdoor function
- Easy to calculate with the public key, but difficult to reverse without the private key
Elliptic curve cryptography (ECC)
- Concerns about RSA being vulnerable to cryptoanalysis
- Another type of trapdoor function
- Can use smaller keys to obtain same security
Public Key Infrastructure
Public Key Infrastructure (PKI) is a technology for authenticating users and devices in the digital world.
- One or more trusted parties digitally sign documents certifying that a particular cryptographic key belongs to a particular user or device
- Key used as an identity for the user in digital networks
Advantage of PKI:
- Scalable data and identity security
- Credibility of keys validated by a third-party
Basic functions of PKI:
- Establish the identity of endpoints on a network
- Encrypt the flow of data via the network's communication channels
What is PKI used for?
- Secure Browsing (via SSL/TLS)
- Securing Email (signing and encrypting messages)
- Secure Code-Signing
- Network Security
- File Security (via Encrypted File Systems)
How is PKI used?
HTTPS:
- Defends against MitM and session hijacking
- Preferred over HTTP (cleartext)
- Why no HTTPS
Authenticating users and computers with SSH.
Email signing and encryption using Pretty Good Privacy (PGP).
Pretty Good Privacy (PGP)
Email signing and ecryption using Pretty Good Privacy (PGP).
OpenPGP is the most current version.
Original PGP developed in the 90s:
- Backwards compatibility means possibility of downgrade attack
- Original PGP considered an insecure encryption method
GPG4Win
Gpg4win (GNU Guard for Windows) is encryption software for files and emails.
- Securely transport emails and files with the help of encryption and digital signatures
- Includes Kleopatra, a certificate manager
- GnuPG is the backend that performs encryption processes
Reflection
Consider the “learning pyramid as shown in the image below. Do you find that matches the way that you learn, or would you weight the activities differently? If so, how?
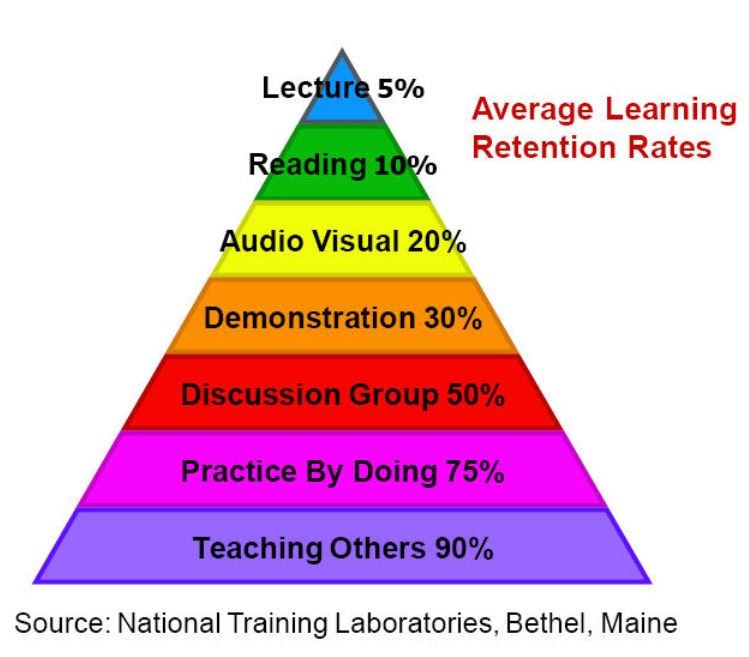
Being a cybersecurity enthusiast and electronics, telecommunications, and computer engineer, I might be more inclined towards hands-on learning and problem-solving, practice by doing and demonstration would likely be more effective than lectures and reading. Discussion groups and teaching others might also be useful for reinforcing and deepening their understanding of the material.
So, in my case, the weight of the activities might be different from the figure above. However, it is important to keep in mind that it's also essential to use a variety of learning activities to ensure comprehensive learning and retention of information.