10 Class 06: Read Cryptography and Data File Encryption - VascoLucas01/cybersecurity-reading-notes GitHub Wiki
Introduction
Cryptography is the practice of encoding information in a manner that it cannot be decoded without access to the required decryption key. Cryptography consists of two main operations:
- Encryption. Transforms plaintext information into ciphertext using an encryption key
- Decryption. Transforms ciphertext back into plaintext using a decryption key
Cryptography has several important goals. First among these is the goal of confidentiality, which corresponds to one of the three legs of the CIA triad. Organizations use encryption to protect sensitive information from prying eyes. The second goal, integrity, also corresponds to one of the three elements of the CIA triad. Organizations use cryptography to ensure that data is not maliciously or unintentionally altered. When we get to the third goal, authentication, the goals of cryptography begin to differ from the CIA triad. Although authentication begins with the letter A, remember that the A in the CIA triad is "availability". Authentication referes to uses of encryption to validate the identity of individuals. The fourth goal, nonrepudiation, ensures that individuals can prove to a third party that a message came from its purported sender.
Historical Cryptography
Historical methods of cryptography predate predate the modern computer age. These methods did not depend on mathematics, as many modern methods do, but rather on some technique for scrambling the text.
- A cipher is a method used to scramble or obfuscate chararcters to hide their value.
- Ciphering is the process of using a cipher to do that type of scrambling to a message.
The two primary types of nonmathematical cryptography, or ciphering methods, are substitution and transposition.
Substitution Ciphers
A substitution cipher is a type of coding of ciphering system that changes one character or symbol into another.
For more information, see the method used in one of the oldest known substitution ciphers called the Caesar cipher.
Additionally, ROT13, or "rotate 13", is another simple substsitution cipher. The ROT13 cipher works the same way as the Caesar cipher but rotates every letter 13 places in the alphabet.
Polyalphabetic Substitution
One of the problems with substitution ciphers is that they did not change the underlying letter and word frequency of the text. One way to combat this was to have multiple substitution alphabets for the same message. Ciphers using this approach are known as polyalphabetic substitution ciphers. For example, you might shift the first letter by three to the right, the second letter by two to the right, and the third letter by one to the left; then repeat this formula with the next three letters.
For more information, see a most famous example of a polyalphabetic substitution from historical times called Vigenere cipher.
Transposition Ciphers
A transposition cipher involves transposing or scrambling the letters in a certain manner. Typically, a message is broken into block of equal size, and each block is then scrambled.
Columnar transposition is a classic example of a transposition cipher.
The Enigma Machine
No discussion of the history of cryptography would be complete without discussing the Enigma machine. The Enigma machine was created by the German government during World War II to provide secure communication between military and political units.
The operator was responsible for configuring the machine to use the code of the day by setting the rotary dials at the top of the machine and configuring the wires on the front of the machine. The ineer workings of the machine implemented a polyalphabetic substitution, changing the substitution for each character of the message.
Steganography
Steganography is the art of using cryptography techniques to embed secret messages within another file. Steganographic algorithms works by making alterations to the least significant bits of the many bits that make up image files. This technique allows communicating parties to hide messages in plain sight.
Steganographers often embed their secret messages within images, video files, or audio files because these files are often so large that the secret key would be easily missed by even the most observant inspector.
Adding digital watermarks to documents to protect intellectual property is accomplished by means of steganography. The hidden information is known only to the file's creator. If someone later creates an unauthorized copy of the content, the water mark can be used to detect the copy and trace the offending copy back to the source.
Goals of Cryptography
Security practitioners use cryptographic systems to meet four fundamental goals: confidentiality, integrity, authentication and nonrepudiation.
Confidentiality
Confidentiality ensures that data remains private in three different situations: when it is at rest, when it is in transit, and when it is in use.
Confidentiality is perhaps the most widely cited goal of cryptosystems - the preservation of secrecy for stored information or for communications between individuals or groups. Two main types of cryptosystems enforce confidentiality.
- Symmetric cryptosystems. It uses a shared key available to all users of the cryptosystem
- Asymmetric cryptosystems. It uses individual combinations of public and private keys for each user of the system.
NOTE: Data in transit is also commonly called data on the wire, referring to the network cables that carry data communications.
When developing a cryptographic system for the purpose of providing confidentiality, you must think about three types of data:
- Data at rest, or stored data, is that which resides in a permanent location awaiting access. Examples of data at rest include data stored on hard drives, backup tapes, cloud storage services, USB devices, and other storage media.
- Data in motion, or data on the wire, is data being transmitted across a network between two systems. Data in motion might be traveling on a corporate network, a wireless network, or the public Internet.
- Data in use is data that is stored in the active memory of a computer system where it may be accessed by a process running on that system.
Data in motion may be susceptible to eavesdropping attacks, whereas data at rest is more susceptible to the theft of physical devices. Data in use may be accessed by unauthorized processes if the operating system does not properly implement process isolation.
Obfuscation is a concept closely related to confidentiality. It is the practice of making it intentionally difficult for humans to understand how code works. This technique is often used to hide the inner workings of software, particularly when it contains sensitive intellectual property.
Integrity
Integrity ensures that data is not altered without authorization. Integrity checks can ensure that stored data was not altered betwwen the time it was created and the time it was accessed. Integrity controls protect against all forms of alteration, including intentional alteration by a third party attempting to insert false information, intentional deletion of portions of the data, and unintentional alteration by faults in the transmission process.
Message integrity is enforced through the use of encrypted message digests, known as digital signatures, created upon transmission of a message. The recipient of the message simply verifies that the message's digital signature is valid, ensuring that the message was not altered in transit. Integrity can be enforced by both public and secret key cryptosystems.
Authentication
Authentication verifies the claimed identity of system users and is major function of cryptosystems.
Nonrepudiation
Nonrepudiation provides assurance to the recipient that the message was originated by the sender and not someone masquerading as the sender. Secret key, or symmetric key, cryptosystems do not provide this guarantee of nonrepudiation.
Cryptographic Concepts
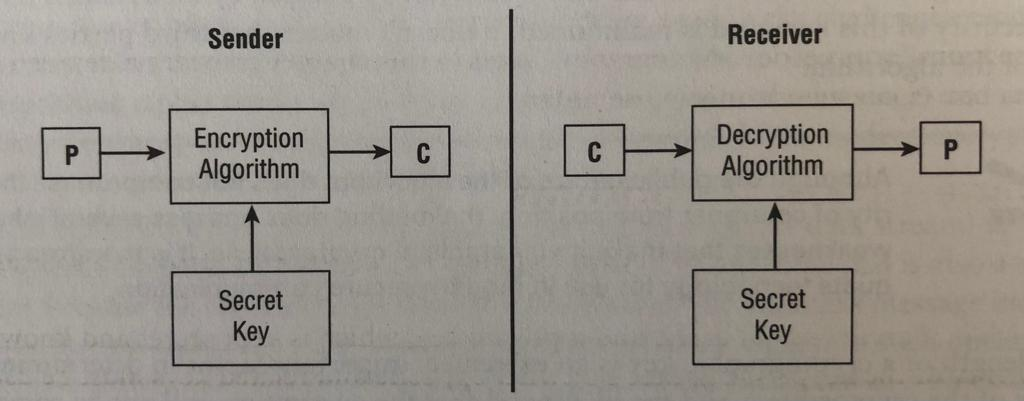
Before a message is put into a coded form, it is known as a plaintext message and is represented by the letter P when encryption functions are described. The sender of a message uses cryptographic algorithm to encrypt the plaintext message and produce a ciphertext message, represented by C. The recipient then uses a predetermined algorithm to decrypt the ciphertext message and retrieve the plaintext version.
Cryptographic Keys
All cryptographic algorithms rely on keys to maintain their security. Every algorithm has a specific key space. The key space is the range of values that are valid for use as a key for a specific algorithm. A key space is defined by its key length. Key length is nothing more than the number is «««os binary bits in the key. The key space is the range between the key that has all 0s and the key that has all 1s.
The Kerchoff principle is that a cryptographic system should be secure even if everything about the system, except the key, is public knowledge. Kerchoff's adherents retort that the opposite approach includes the dubious practice of "security through obscurity" and believe that publci exposure produces more activity and exposes more weaknesses more readily, leading to the abandonment of insufficiently strong algorithms and quicker adoption of suitable ones.
Different types of algorithms require different types of keys. In private key (or secret key) cryptosystems, all participants use a single shared key. In public key cryptosystems, each participant has their own pair of keys. Cryptographic keys are sometimes referred to as cryptovariables.
The art of creating and implementing secret codes and ciphers is known as cryptography. This practice is paralleled by the art of cryptanalysis - the study of methods to defeat codes and ciphers. Together, cryptography and cyptanalysis are commonly referred to as cryptology. Specific implementations of a code or cipher in hardware and software are known as cryptosystems.
Ciphers
Ciphers are the algorithms used to perform encryption and decryption operations. Cipher suites are the sets of ciphers and key lengths supported by a system. Modern ciphers fit into two major categories, describing their method of operation:
- Block ciphers operate on "chunks", or blocks, of a message and apply the encryption algorithm to an entire message block at the same time.
- Stream ciphers operate on one character or bit of a message at a time.The Caesar cipher is an example of a stream cipher.
Modern Cryptography
Modern cryptosystems use computationally complex algorithms and long cryptographic keys to meet the cryptographic goals of confidentiality, integrity, authentication, and nonrepudation. The following sections cover the roles of cryptographic keys play in the world of data security and examine three types of algorithms commonly used today:
- Symmetric key
- Encryption algorithms
- Asymmetric key encryption algorithms
- Hashing algorithms
Cryptographic Secrecy
In the early days of cryptography, one of the predominant principles was "security through obscurity". Some cryptographers though the best way to keep an encryption algorithm secure was to hide the details of the algorithm from outsiders. Old cryptosystems required communicating parties to keep the algorithm used to encrypt and decrypt messages secret from third parties. Any disclosure of the algorithm could lead to compromise of the entire system by an adversary.
Modern cryptosystems do not rely on the secrecy of their algorithms. In fact, the algorithms for most cryptographic systems are widely available for public review in the accompanying literature and on the Internet. Opening algorithms to public scrutiny actually improves their security. Widespread analysis of algorithms by the computer security community allows practitioners to discover and correct potential security vulnerabilities and ensure that the algorithms they use to protect their communications are secure as possible.
The lenght of a cryptographic key is an extremely important factor in determining the strength of the cryptosystem and the likelihood that the encryption will not be compromised through cryptanalytic techniques.
Symmetric Key Algorithms
Symmetric key algorithms rely on a "shared key" encryption key that is distributed to all members who participate in the communications. This key is used by all parties to both encrypt and decrypt messages, so the sender and the receiver both possess a copy of the shared key.
Symmetric key cryptography has several weaknesses:
- Key distribution is a major problem
- Symmetric key cryptography does not implement nonrepudiation
- The algorithm is no scalable
- Keys must be regenerated often
Asymmetric Key Algorithms
Asymmetric key algorithms, also known as public key algorithms, provide a solution to the weaknesses of symmetric key encryption. In these systems, each user has two keys: a public key, which is shared with all users, and a private key, which is kept secret and known only to the owner of the keypair.
Asymmetric key algorithms also provide support for digital signature technology.
The following is a list of the major strenghts of asymmetric key cryptography:
- The addition of new users requires the generation of only one public-private key pair
- Users can be removed far more easily from asymmetric systems
- Key regeneration is required only when when a user's private key is compromised
- Asymmetric key encryption can provide integrity, authentication, and nonrepudiation
- Key distribution is a simple process
- No preexisting communication link needs to exist
The major weakness of public key cryptography is its slow speed of operation.
Hashing Algorithms
In the previous point, you learned that public key cryptosystems can provide digital signature capability when used in conjunction with a message digest. Message digests are summaries of a message's content produced by a hashing algorithm. It is extremely difficult, if not impossible, to derive a message from an ideal hash function, and it is very unlikely that two messages will produce the same hash value. Cases where a hash function produces the same value for two different methods are known as collisions, and the existence of collisions typically leads to the deprecation of a hashing algorithm.
Symmetric Cryptography
In the following topics, we'll take an in-depth look at several common symmetric cryposystems:
- Data Encryption Standard (DES)
- Triple DES (3DES)
- Advanced Encryption Standard (AES)
Data Encryption Standard
The U.S. government published the Data Encryption Standard in 1977 as a proposed standard cryptosystem for ll government communications. Because of flaws in the algorithm, cryptographers and the federal government no longer consider DES secure. DES was superseded by the Advanced Encryption Standard in December 2001. It is still important to understand DES because it is the building block of Triple DES (3DES), a strong encyption algorithm discussed in the next section.
DES is a 64-bit block cipher that has five modes of operation:
- Electronic Codebook (ECB) mode
- Cipher Block Chaining (CBC)
- Cipher Feedback (CFB)
- Output Feedback (OFB)
- Counter (CTR) mode
All of the DES modes operate on 64 bits of plaintext at a time to generate 64-bit blocks of ciphertext. The key used by DES is 56 bits long.
DES uses a long series of exclusive or (XOR) operations to generate the ciphertext. This process is repeated 16 times for each encryption/decryption operation. Each repetition is commonly referred to as a round of encryption, explaining the statement that DES performs 16 rounds of encryption.
As mentioned, DES uses a 56-bit key to drive the encryption and decryption process. However, you may read in some literature that DES uses 64-bit key. This is not an inconsistency - there's a perfectly logical explanation. The DES specification calls for 64-bit key. However, of those 64 bits, only 56 actually contain keying information. The remaining 8 bits are supposed to contain parity information to ensure that the other 56 bits are accurate. In practice, however, those parity bits are rarely used. You should commit the 56-bit figure to memory.
Electronic Codebook Mode
Electronic Codebook (ECB) mode is the simplest mode to understand and the least secure. Each time the algorithm processes a 64-bit block, it simply encrypts the block using the chosen secret key. This means that if the algorithm encounters the same block multiples times, it will produce the same encrypted block.
Cipher Block Chaining Mode
In Cipher Block Chaining (CBC) mode, each block of unencrypted text is combined with the block of ciphertext immediately precending it before it is encrypted using the DES algorithm. The decryption process simply decrypts the ciphertext and reverses the encryption operation.
CBC uses an initialization vector (IV), which is a randomly selected values that is used to start the encryption process. CBC takes the IV and combines it with the first block of the message using an operation known as the exclusive or (XOR), producing a unique output every time the operation is performed.
Cipher Feedback Mode
Cipher Feedback (CFB) mode, is the streaming cipher version of CBC. In other words, CFB operates against data produced in real time. However, instead of breaking a message into block, it uses memory buffers of the same block size. As the buffer comes full, it is encrypted and then sent to the recipients.
Output Feedback Mode
In Output Feedback (OFB) mode, DES operates in almost the same fashion as it does in CFB mode. However, instead of XORing an encrypted version version of the previous block of ciphertext, DES XORs the plaintext with a seed value. Future seed values are derived by running the DES algorithm on the previous seed value.
Counter Mode
DES that is run in Counter (CTR) mode uses a stream cipher similar to that used in CFB and OFB modes. However, instead of creating the seed value for each encryption/decryption operation from the results of the previous seed values, it uses a simple counter that increments for each operation. As with OFB mode, errors do not propagate in CTR mode.
CTR mode allows you to break an encryption or decryption operation into multiple independent steps. This makes CTR mode well suited for use in parallel computing.
Triple DES
As mentioned in the previous points, the Data Encryption Standard's 56-bit key is no longer considered adequate in the face of modern cryptanalytic techniques and supercomputing power. However, an adapted version of DES, Triple DES (3DES), uses the same algorithm to produce a more secure encryption.
There are four versions of 3DES. The first simply encrypts the plaintext three times, using three different keys: K1, K2, and K3. It is known as DES-EEE3 mode (the Es indicate there are three encryption operations, whereas the numeral 3 indicates that three different keys are used). DES-EEE3 can be expressed using the following notation, where E(K,P) represents the encryption of plaintext P with the key K:
E(K1,E(K2,E(K3,P)))
DES-EEE3 has an effective key length of 168 bits.
The second variant (DES-EDE3) also uses three keys but replaces the second encryption operation with a decryption operation.
E(K1,D(K2,E(K3,P)))
The third version of 3DES (DES-EEE2) uses only two keys, K1 and K2, as follows:
E(K1,E(K2,E(K1,P)))
The fourth variant of 3DES (DES-EDE2) also uses two keys but uses a decryption operation in the middle, represented by the D(K,C) function, where K is the decryption key and C is the ciphertext to be decrypted.
E(K1,D(K2,E(K1,P)))
Both the third and fourth variants have an effective key length of 112 bits.
Advanced Encryption Standard
In October 2000, the National Institute of Standards and Technology announced that the Rijndael block cipher had been chosen as the replacement for DES. In November 2001, NIST released FIPS 197, which mandated the use of AES/Rijndael for the encyption of all sensitive but unclassified data by the U.S. government.
The AES cipher allows the use of three key lengths: 128 bits, 192 bits, and 256 bits. AES only allows the processing of 128-bit blocks, but Rijndael excedeed this specification, allowing cryptographers to use a block size equal to the key lenght. The number of encryption rounds depends on the key length chosen:
- 128-bit keys require 10 rounds of encryption
- 192-bit keys require 12 rounds of encryption
- 256-bit keys require 14 rounds of encryption
Symmetric Key Management
Because cryptographic keys contain information essential to the security of the cryptosystem, it is incumbent upon cryptosystem users and administrators to take extraordinary measures to protect the security of the keying material. These measures are collectively known as key management practices. They include safeguards surrounding the creation, distribution, storage, destruction, recovery, and scrow of secret keys.
Creation and Distribution of Symmetric Keys
As previouly mentioned, key exchange is one of the major problems underlying symmetric encryption algorithms. Key exchange is the secure distribution of the secret keys required to operate the algorithms. The three main methods used to exchange secret keys securely are:
- Offline distribution
- Public key encryption
- Diffie-Hellman
Storage and Destruction of Symmetric Keys
Another major challenge with the use of symmetric key cryptography is that all of the keys used in the cryptosystem must be kept secure. This includes following best practices surrounding the storage of encryption keys:
- Never store an encryption key on the same system where the encrypted data resides. This just makes it easier for the attacker!
- For sensitive keys, consider providing two different individuals with half of the key. They then must collaborate to re-create the entire key. This is known as the principle of split knowledge.
When a user with knowledge of a secret key leaves the organization or is no longer permitted access to material protected with that key, the keys must changed, and all encrypted materials must be reencypted with the new keys.
Key Escrow and Recovery
Cryptography is a powerfool tool. Like most tools, it can be used for a number of beneficent purposes, but it can be used with malicious intent. To gain a handle on the explosive growth of cryptographic technologies, governments arount the world have floated ideas to implement key escrow systems. These systems allow the government, under limited circumstances such as a court order, to obtain the cryptographic key used for a particular communication from a central storage facility.
There are two major approaches to key escrow that have been proposed over the past decade:
- Fair Cryptosystems
- Escrowed Encryption Standard
Asymmetric Crytography
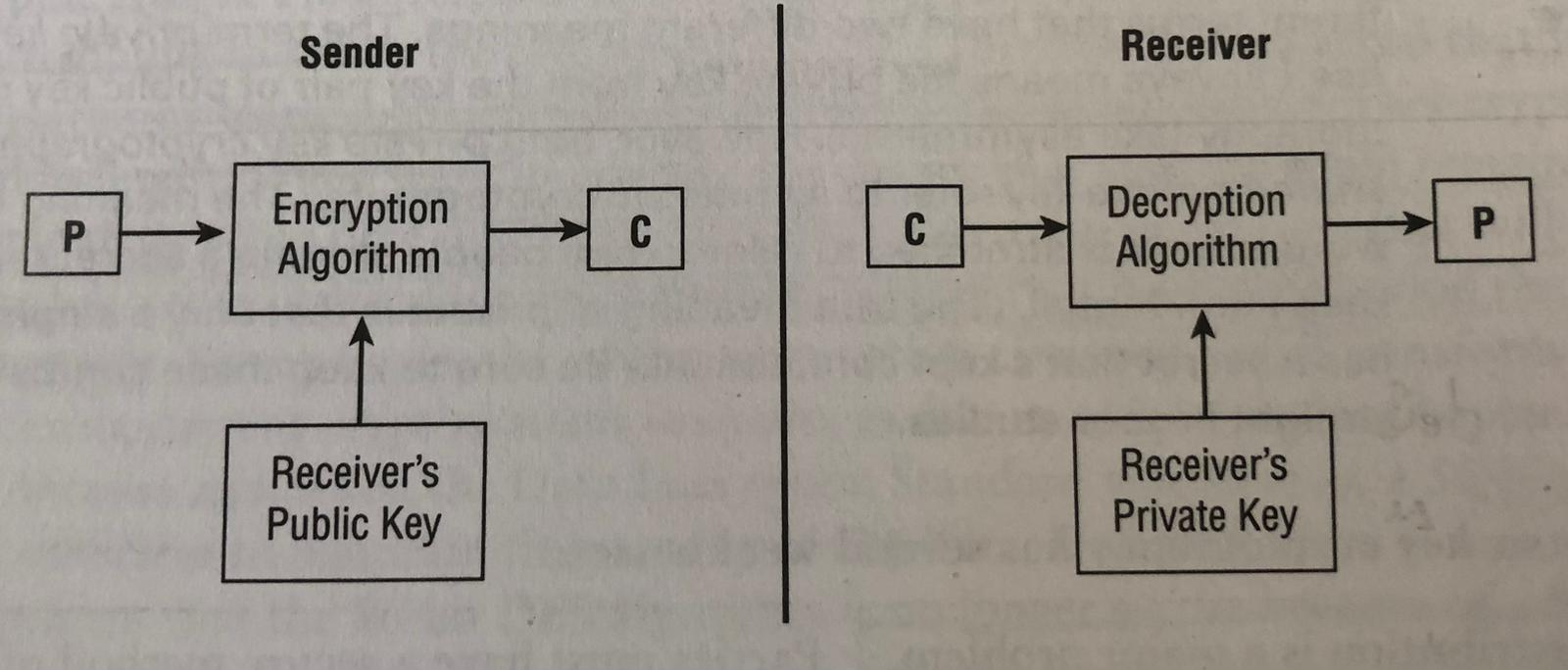
Recall from earlier in this chapter that public key cryptosystems rely on pairs of keys assigned to each user of the cryptosystem. Every user maintains both public key and a private key. As the names imply, public key cryptosystem users make their public keys freely available to anyone with whom they want to communicate. The private key, on the other hand, is reserved for the sole use of the individual who owns the keys.
The sender encrypts the plaintext message (P) with the recipient's public key to create the ciphertext (C). When the recipient opens the ciphertext message, they decrypt it using their private key to re-create the original plaintext message.
Once the sender encrypts the message with the recipient's public key, no user can decrypt that message without knowing the recipient's private key. This is the beauty of public key cryptography - public jeys can be freely shared using unsecured communications and then used to create secure communications channels between users previously unknown to each other.
RSA
The most famous public key cryptosystem is named after its creators. In 1977, Ronald Rivest, Adi Shamir, and Leonard Adleman proposed the RSA public key algorithm that reamins a worldwide standard today.
The RSA algorithm depends on the computational difficulty inherent in factoring large prime numbers. each user of the cryptosystem generates a pair of public and private keys using the algorithm.
Elliptic Curve
In 1985, two mathematicians, Neal Koblitz from the University of Washington and Victor Miller from IBM, independently proposed the application of elliptic curve cryptography (ECC) theory to develop secure cryptographic systems.
Hash Functions
Later, you'll learn how cryptosystems implement digital signatures to provide proof that a message originated from a particular use rof the cryptosystem and to ensure that the message was not modified while in transit betwwen two parties. Before you can completely understand that concept, we must first explain the concept of hash functions.
Hash functions have a very simple purpose - they take a potentially long message and generate a unique output value derived from the content of the message. This value is commonly referred to as the message digest. Message digest can be regenerated by the sender of a message and transmitted to the recipient along with the full message for two reasons.
- The recipient can use the same hash function to recompute the message digest from the full message
- The message digest can be used to implement signature algorithm
There are five basic requirements for a cryptographic hash function:
- They accept an input of any lenght
- They produce an output of a fixed length, regardless of the length of the input
- The hash value is relatively easy to compute
- The hash function is one-way
- The hash function is collision free
SHA
The Secure Hash Algorithm (SHA) and its sucessors, SHA-1, SHA-2, and SHA-3, are government standard hash functions promoted by the National Institute of Standards and Technology (NIST) and are specified in an official government publication - the Secure Hash Standard (SHS), also known as Federal Information Processing Standard (FIPS).
SHA-1 takes an input of virtually any length and produces a 160-bit message digest. The SHA-1 algorithm processes a message in 512-bit blocks. Therefore, if the message length is not multiple of 512, the SHA algorithm pads the message with additional data until the length reaches the next highest multiple 512.
Cryptanalytic attacks demosntrated that there are weaknesses in the SHA-1 algorithm. This led to the creation of SHA-2, which has four variants:
- SHA-256 produces a 256-bit message digest using 512-bit block size
- SHA-224 uses a truncated version of the SHA-256 hash to produce a 224-bit message digest using a 512-bit block
- SHA-512 produces a 512-bit message digest using a 1,024-bit block size
- SHA-384 uses a truncate version of the SHA-512 hash to produce a 384-bit digest using a 1,024-bit block size.
The cryptographic community generally considers SHA-2 algorithms secure, but theu theorically suffer from the same weaknesses as the SHA-1 algorithm. In 2015, the federal government announced the release of the Keccak algorithm as the SHA-3 standard. The SHA-3 suite was developed to serve as drop-in replacement for the SHA-2 hash functions, offering the same variants and hash lenghts using a more secure algorithm.
MD5
In 1991, Ron Rivest released the next version of his message digest algorithm, which he called MD5. It also processes 512-bit blocks of the message, but it uses four distinct rounds of computation to produce a digest of the same length as the earlier MD2 and MD4 algorithms (128 bits).
MD5 implements security features that reduce the speed of message digest production significantly. Unfortunately, recent cryptanalytic attacks demonstrated that the MD5 protocol is subject to collisions, preventing its use for ensuring message integrity.
Digital Signatures
Once you have chosen a cryptographically sound hashing algorithm, you can use it to implement a digital signature system. Digital signature infrastructures have two distinct goals:
- Digitally signed messages assure the recipient that the message truly came from the claimed sender. They enforce nonrepudiation.
- Digitally signed messages assure the recipient that the message was not altered while in transit between the sender and recipient.
Digital signature algorithms rely on a combination of the two major concepts already convered in this Class 06: Read Cryptography and Data File - public key cryptography and hashing functions.
Note that the digital signature does not provide any privacy in and of itself.
HMAC
The Hashed Message Authentication Code (HMAC) algorithm implements a partial digital signature - it guarantees the integrity of a message during transmission, but it does not provide nonrepudiation.
HMAC can be combined with any standard message digest generation algorithm, such as SHA-3, by using a shared secret key.
Because HMAC relies on a shared secret key, it does not provide any nonrepudiation functionality.
Which Key Should I Use?
- If you want to encrypt a message, use the recipient's public key
- If you want to decrypt a message sent to you, use your private key
- If you want to digitally sign a message you are sending to someone else, use your private key
- If you want to verify the signature on a message sent by someone else, use the sender's public key
Digital Signature Standard
The National Institute of Standards and Technology specifies the digital signature algorithms acceptable for the federal governmnent use in Federal Informaiton Processing Standard (FIPS) 186-4, also known as the Digital Signature Standard (DSS). This document specifies that all federally approved digital signature algorithms must use the SHA-3 hashing functions.
DSS also specifies the encryption algorithms that can be used to support a digital signature infrastructure. There are three currently approved standard encryption algorithms:
- The Digital Signature Algorithm (DSA) as specified in FIPS 186-4
- The Rivest, Shamir, Adleman (RSA) algorithm as specified in ANSI X9.31
- The Elliptic Curve DSA (ECDSA) as specified in ANSI X9.62
*Public Key Infrastruture
The major strength of public key encryption is its ability to facilitate communication between parties previously unknown to each other. This is made possible by the public key infrastructure (PKI) hierarchy of trust relationships. These trusts permit combining asymmetric cryptography with symmetric cryptography along with hashing and digital certificates, giving us a hybrid cryptography.
Certificates
Digital certificates provide communicating parties with asssurance that the people they are communicating with truly are who they claim to be. Digital certificates are essentially endorsed copies of an individual's public key. When users verify that certificate was signed by a trusted certificate authority (CA), they know that the public key is legitimate.
Certificates may be issued for a variety of purposes. These include providing assurance for the public keys of:
- Computers/machines
- Individual users
- Email addresses
- Developers
Certificate Authorities
Certificate authorities (CAs) are the glue that binds the public key infrastructure together. These neutral organizations offer notarization services for digital certificates. To obtain a digital certificate from a reputable CA, you must prove your identity to the satisfaction of the CA.
Registration authorities (RAs) assist CAs with the burden of verifying users' identities prior to issuing digital certificates. They do not directly issue certificates themselves, but they play an important role in the certification process, allowing CAs to remotely validate user identities.
Certificate authorities must carefully protect their own private keys to preserve their trust relationships. To do this, they often use an offline CAS to protect their root certificate, the top-level certificate for their entire PKI. This offline CA is disconnected from networks and powered down until it is needed. The offline CA uses the root certificate to create subordinate intermediate CAs that serve as the online CAs used to issue certificates on a online basis.
In the CA trust model, the use of a series of intermediate CAs is known as certificate chaining. To validate a certificate, the browser verifies the identity of the intermediate CA(s) first and then traces the path back to a known root CA, verifying the identity of each link in the chain of trust.
Certificate authorities do not need to be third-party service providers. Many organizations operate internal CAs that provide self-signed certificates for use inside an organziation.
Certificate Generation and Destruction
The technical concepts behind the public key infrastructure are relatively simple. In the following points, I'll cover the processes used by certificate authorities to create, validate, and revoke client certificates.
Enrollment
When you want to obtain a digital certificate, you must first prove your identity to the CA in some manner; this process is called enrollment. As mentioned above in the previous point, this sometimes involves physically appearing before an agent of the certification authority with the appropriate identifications documents. Some certificate authorities provide other means of verification, including the use of credit report data and identity verification by trusted community leaders.
Once you've satisfied the certificate authority regarding your identity, you provide them with your public key in the form of a Certificate Signing Request (CSR). The CA next creates an X.509 digital certificate containing your identifying information and a copy of your public key. The CA then digitally signs the certificate using the CA's private key and provides you with a copy of your signed digital certificate. You may then safely distribute this certificate to anyone with whom you want to communicate securely.
Certificate authorities issue different types of certificates depending upon the level of identity verification that they perform. The simplest, and most common, certificates are Domain Validation (DV) certificates, where teh CA simply verifies that the certificate subject has control of the domain name. Extended Validation (EV) certificates provide a higher level of assurance and the CA takes steps to verify that the certificate owner is a legitimate business before issuing the certificate.
Verification
When you receive a digital certificate from someone with whom you want to communicate, you verify the certificate by checking the CA's digital signature using the CA's public key. Next, you must check and ensure that the certificate was not revoked using certificate revocation list (CRL) or the Online Certificate Status Protocol (OCSP). At this point, you may assume that the public key listed in the certificate is authentic, provided that it satisfies the following requirements:
- The digital signature of the CA is authentic
- You trust the CA
- The certificate is not listed on a CRL
- The certificate actually contains the data you are trusting
The last point is a subtle but extremely important item. Before you trust an identifying piece of information about someone, be sure that it is actually contained within the certificate.
Certificate pinning approaches instruct browsers to attach a certificate to a subject for an extended period of time. When sites use certificate pinning, the browser associates that site with their public key. This allows users or administrators to notice and intervene if a certificate unexpectedly changes.
Revocation
Occasionally, a certificate authority needs to revoke a certificate. This might occur for one of the following reasons:
- The certificate was compromised
- The certificate was erroneously issued
- The details of the certificate changed
- The security association changed
The revocation request grace period is the maximum response time within which the CA will perform any requested revocation. This is defined in the certificate practice statement (CPS). The CPS states the practices a CA employs when issuing or managing certificates.
You can use three techniques to verify the authenticity of certificates and identify revoked certificates:
- Certificate Revocation Lists. Certificate revocation lists (CRLs) are maintained by the various certificate authorities and contain the serial numbers of certificates that have been revoked along with the date and time the revocation went into effect.
- Online Certificate Status Protocol (OCSP). This protocol eliminates the latency inherent in the use of certificate revocation lists by providing a means for real-time certificate verification.
- Certificate Stapling. The primary issue with OCSP is that it places a significant burden on the OCSP servers operated by certificate authorities. It is an extension to the Online Certificate Status Protocol that relieves some of the burden placed upon certificate authorities by the original protocol. It is common to have stapled certificates with a validity period of 24 hours. That reduces the burden on a OCSP server from handling one request per user over the course of the day, which could be millions of requests, to handling one request per certificate per day.
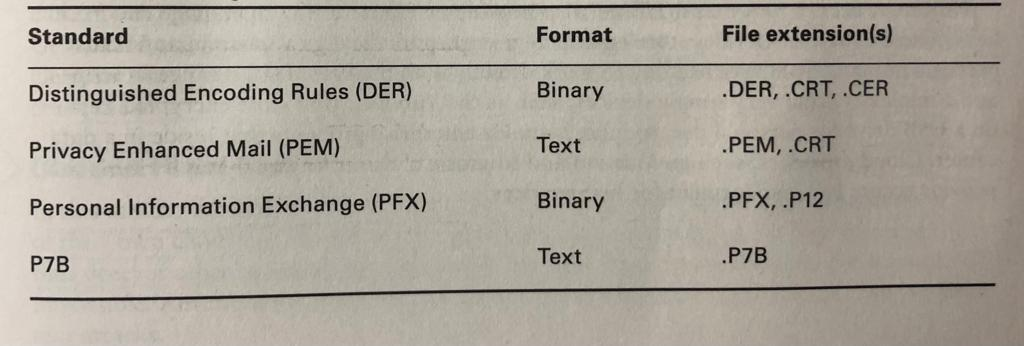
Certificate Formats
Asymmetric Key Management
When working with the public key infrastructure, it's important that you comply with several best practice requirements to maintain the security of your communications.
First, choose your encryption system wisely. As you learned earlier, "security through obscurity" is not an appropriate approach. Choose an encryption system with an algorithm in the public domain that has thorughly vetted by industry experts.
You must also select your keys in an appropriate manner. Use a key length that balances your security requirements with performance considerations. Also, ensure that your key is truly random, or, in cryptographic terms, that it has sufficient entropy. You shloud also understand the limitations of your cryptographic algorithm and avoid the use of any known weak keys.
When using public key encryption, keep your private key secret!
Retire keys when they've served a useful life. Many organizations have mandatory key rotation requirements to protect against undetected key compromise.
Back up your key! If you loose the file containing your private key because of data corruption, disaster, or other circumstances, you'll certainly want to have a backup available. You may want to either create your own backup or use a jey escrow service that maintains the backup for you. In either case, ensure that the backup is handled in a secure manner.
Hardware security modules (HSMs) also provide an effective way to manage encryption keys. These hardware devices store and manage encryption keys in a secure manner that prevents humans from ever needing to work directly with the keys. HSMs range in scope and complexity from very simple devices, such as YubiKey, that store encrypted keys on a USB drive for personal use, to more complex enterprise products that reside in a data center.
Cryptographic Attacks
If time has taught us anything, it is that people frequently do things that other people thought were impossible. Every time a new code or process is invented that is thought to be unbreakable, someone comes up with a metohd of breaking it.
Let's look at some common code-breaking techniques.
Brute Force
This method simply involves trying every single possible key. It is guaranteed to work, but it is likely to take so long that it is simply not usable.
Frequency Analysis
Frequency analysis involves looking at the blocks of an encrypted message to determine if any common pattherns exists.
Known Plain Text
This attack relies on the attacker having pairs of known plaintext along with the corresponding ciphertext.
Chosen Plain Text
In this attack, the attacker obtains the ciphertexts corresponding to a set of plaintexts of their own choosing. This allows the attacker attempt to derive the key used and thus decrypt other messages encrypted with that key.
Related Key Attack
This is like a chosen plaintext attack, except the attacker can obtain cupertexts encrypted under two different keys.
Birthday Attack
This is an attack on cryptographic hashes, based on something called the birthday theorem.
Downgrade Attack
A downgrade attack is sometimes used against secure communications such as TLS in an attempt to get the user or system to inadvertently shift to less secure cryptographic modes. The idea is to trick the user into shifting to a less secure version of the protocol, one that might be easier to break.
Rainbow Tables, Hashing, and Salting
Rainbow table attacks attempt to reverse hashed password value by precomputing the hashes of common passwords. The attacker takes a list of common passwords and runs them through the hash function to generate the rainbow table. They then search trough lists of hashed values, looking for matches to the rainbow table. The most common approch to preventing these attacks is salting, which adds a randomly generated value to each password prior hashing.
Key stretching is used to create encryption keys from passwords in a stronger manner. Key stretching algorithms, such as the Password Based Key Derivation Function v2 (PBKDF2), use thousands of iterations of salting and hashing to generate encryption keys that are resilient against attacks.
Exploiting Weak Keys
There are also scenarios in which someone is using a good cryptographic algorithm (like AES) but it has implemented in a weak manner - for example, using weak generation. A classic example is the Wireless Equivalent Privacy (WEP) protocol.
Exploiting Human Error
Human error is one of the major causes of encryption vulnerabilites. If an email is sent using an encryption scheme, someone else may send it in the clear. If a cryptanalyst gets ahold of both messages, the process of decoding future messages will be considerably simplifies.
Questions
1. You have been made responsible for the company’s file server. How would you preserve the three elements of the CIA triad?
To preserve confidentiality, I would need to implement some access controls, such as usernames and passwords, and limiting user privileges to only what is required for their job responsibilities by following the concept of least priviledge.
To preserve integrity, I would need to ensure that the data stored on the file server is not modified, deleted, or corrupted without authorization. One way to achieve this is by implementing hashing algorithms and digital signatures.
To preserve availability, I would need to ensure that the file server is accessible to authorized users everytime they want. This can be achieved by implementing redundant systems and by regularly monitoring the system to detect and address any issues that may arise.
2. Explain how hashing verifies data integrity using non-technical terms.
Imagine you have a puzzle with 10000 pieces. You put the puzzle together and take a photo of it to send to your friend. To ensure that the puzzle arrives at your friend's house in the same condition as when you sent it, you could create a unique mark on the back of the photo that only you know. When your friend receives the photo, they can check the mark to make sure it matches the original mark you created. If the mark doesn't match, they know that the puzzle has been altered or damaged during shipment.
3. How is hashing and encryption different?
Encryption is the process of converting data into an unreadable format, called ciphertext, which can only be decoded with a specific key or password. The purpose of encryption is to protect data from unauthorized access or interception.
Hashing is the process of converting data into a fixed-length sequence of characters or numbers, called a hash. The purpose of hashing is to verify the integrity of data by checking if it has been modified or not. Hashing does not protect data from unauthorized access but only verifies if the data has been altered or not.