10 Class 03: Learning Journal - VascoLucas01/cybersecurity-reading-notes GitHub Wiki
Introduction
[Date: 2023/04/14]
In this Class 03: Learning Journal, I am going to talk about the main ideas/concepts covered in the cyber risk analysis lecture.
After that, I am going to make a refletion based on the question referred at the end of this page.
Today I Learned
Cyber risk analysis is a critical process for cybersecurity practitioners to understand and mitigate potential threats to an organization's information systems and assets. This involves identifying, assessing, mitigating, monitoring and report, and prioritizing potential risks, vulnerabilities, and threats that could compromise the confidentiality, integrity, and availability of sensitive data. By conducting a thorough cyber risk analysis, practitioners can develop a comprehensive cybersecurity strategy and implement appropriate controls to reduce the likelihood and impact of cyber-attacks. Additionally, by regularly reviewing and updating the risk analysis, practitioners can ensure that the organization's cybersecurity measures remain effective and up-to-date in the face of evolving threats. Implementing cyber risk analysis in an organization is crucial to establish a proactive approach to cybersecurity and prevent potential financial and reputational damage caused by cyber-attacks.
The first concepts addressed in the lecture about this topic were:
- Risk. It is the likelihood and impact (or consequence) of a threat actor exploiting a vulnerability. Indeed, it can be seen as the core mission of cybersecurity professionals that aim to manage and mitigate risk for the employer or client.
- Vulnerability. It is a weakness that could be triggered accidentally or exploited intentionally to cause a security breach.
- Threat. It is the potential for someone or something to exploit a vulnerability and breach security. A threat may be intentional or unintentional
NOTE: A zero-day vulnerability is a vulnerability that is known, but there are no methods or security controls to mitigate that vulnerability. It is important for an organization to prevent zero-day vulnerabilities disclosure.
The People, Process and Technology Framework (PPT)
The People, Process and Technology Framework "is used when making decisions about acquiring or implementing new technology and can help bring harmony within a company"
What is Risk Management Lifecycle (ISC2)?
The Risk Management Lifecycle pass through some important processes:
- Risk Assessment
- Categorize, Classify and Value Assets
- Know/Identify Threats and Vulnerabilities
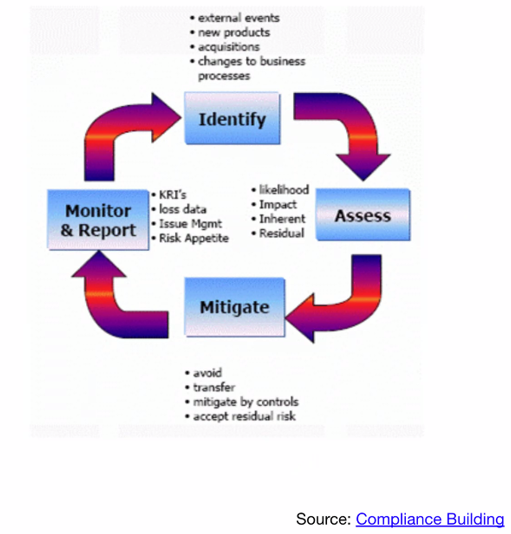
- Identify. It is here where an organization looks for any external events, new products or acquisitions.
- Assess. It is here where an organization measures the likelihood and impact of inherent and residual risks.
- Mitigate. It is here where an organization try to avoid, tranfer, mitigate by controls or even accept a specific risk.
- Monitor & Report. It is here where professional analysts use tools like KRI's to monitor risk appetite.
NOTE: Risk Appetite is the amount of risk an organization is willing to take before choosing some way to mitigate it.
Risk Assessment
- Quantitative Risk Assessment
- Qualitative Risk Assessment
Regarding Quantitative Risk Assessment, it is important to mention the process that most quantitative assessments follow:
1. Asset Value (AV). How much is the asset worth? 2. Annual Rate of Ocorrence (ARO). How often that risk will occur per year? 3. Exposure Factor (EF). Percentage of AV lost? 4. Single Loss Expectancy (SLE). What does it cost of it happens once?; It is calculated by multiplying AV x EF 5. Annualized Loss Expectancy (ALE). What it cost per year if we do nothing?
NOTE: Total Cost of Ownership (TCO) is the mitigation cost. upfront + ongoing cost
Regarding Qualitative Risk Assessment:
- Softer approach, does not use data qualification
- Rating system is used instead
- Requires judgements, best practices, intuition and experience
- Methods, such as brainstorming, delphi technique, questionnaires, focus groups, surveys, checklists, interviews, 1:1 meetings, etc
Risk Response
- Reduce
- Avoid
- Transfer
- Accept/Reject
Quantitative Risk Analysis
- Vulnerability + Threat = Risk
- Impact x Likelihood = Risk
- This involves assigning monetary values to risk
Risk Management Options
- Risk Acceptance. Level of risk is known and accept
- Risk Avoidance. Remove opportunity for risk to cause loss
- Risk Mitigation. Utilize security controls to reduce risk acceptance levels
- Risk Transference. Pay an external party to accept the finance impact of a given risk
What is cyber hygiene?
Cyber hygiene includes practices and precautions to facilitate keeping sensitive data organized, safe, and secure from exfiltration and attack.
But how do security teams work to mitigate risk for their employees and clientele? In fact, they regularly evaluate for cyber hygiene, perform vulnerability scans and assessments, and thereby generate risk assessments which facilitate better organizational decision making.
The principal question here for this particular topic of Risk Cyber Analysis is:
- Can risk be eliminated?
Cyber risk can't fully eliminated, but it can significantly mitigated.
Residual risk consists of the risk remaining after security control have been put in place as a means of risk mitigation.
RMF, or Risk Management Framework is a voluntary guidance, based on existing standards, guidelines, and practices for organizations to better manage and reduce cybersecurity risk.
Reflection
What are your motivations for learning?
As a cyber security enthusiast, I am motivated to learn and acquire knowledge in this field to make a positive impact on society. Today's learning has reinforced my passion for this field, as I have gained a deeper understanding of the current threats and risks in the digital world, as well as the methods and techniques used to mitigate them.
I am driven by the desire to protect people and systems from external threats and risks, and I believe that through continuous learning and improvement, I can contribute to achieving this goal. This motivates me to stay up-to-date with the latest trends and technologies in the field of cyber security, and to seek out opportunities for hands-on experience and practical application.
Actually, my motivation for learning in the field of cyber security stems from a desire to make a meaningful contribution to society by protecting individuals and organizations from the harm caused by cyber attacks.