10 Class 01: Read Strategic Policy Development - VascoLucas01/cybersecurity-reading-notes GitHub Wiki
Introduction
Strategic policy development refers to the process of creating and implementing policies that help organizations achieve their long-term goals and objectives. This involves conducting research, analyzing data, identifying trends, and assessing the strengths and weaknesses of various options. The resulting policies can cover a wide range of areas, such as finance, human resources, marketing, or operations.
Effective strategic policy development is critical for organizations to stay competitive and adapt to changing circumstances in today's fast-paced and complex business environment. By having well-crafted policies in place, organizations can improve their decision-making, reduce risks, increase efficiency, and ensure that all stakeholders are aligned towards achieving common goals.
In today's day-to-day, stategic policy development is especially important for businesses and governments that are facing new challenges and opportunities arising from globalization, technological advances, climate change, and other complex issues. It requires a deep understanding of the business landscape and the ability to anticipate future trends and needs.
History of SOC 2
Before talking about SOC 2 itself, it is important to understand a little about its history.
Before the introduction of SOC 2, service organizations were audited using the SAS 70, or Statement of Auditing Standards No. 70, reporting standard. SAS 70 audits were performed by Certified Public Accountants (CPAs) and focused primarily on reporting the effectiveness of internal financial controls. However, over time, SAS 70 audits began to be used to evaluate an organization's controls around information security more broadly.
In 2010, the American Institute of Certified Public Accountants (AICPA) introduced SOC 1 and SOC 2 reports to address the growing need for external validation and communication of an organization security posture. While SOC 1 reports still focus on controls impacting financial reports, SOC 2 reports are based on audits against the Trust Services Criteria (TSC) standard, which assesses an organization's controls over security, availability, processing integrity, confidentiality, and privacy. SOC 2 compliance is ideal for organizations looking to improve their maturity around business processes and security simultaneously.
What is SOC 2?
SOC 2, or Service Organization Control 2, is an auditing process that evaluates an organization's ability to securely manage and protect sensitive customer data. It is quite relevant to SaaS businesses, but also to many others who store their customers's data. The SOC 2 framework was developed by the American Institute of Certified Public Accountants (AICPA) and outlines the criteria for assessing an organization's controls over security, availability, processing integrity, confidentiality, and privacy.
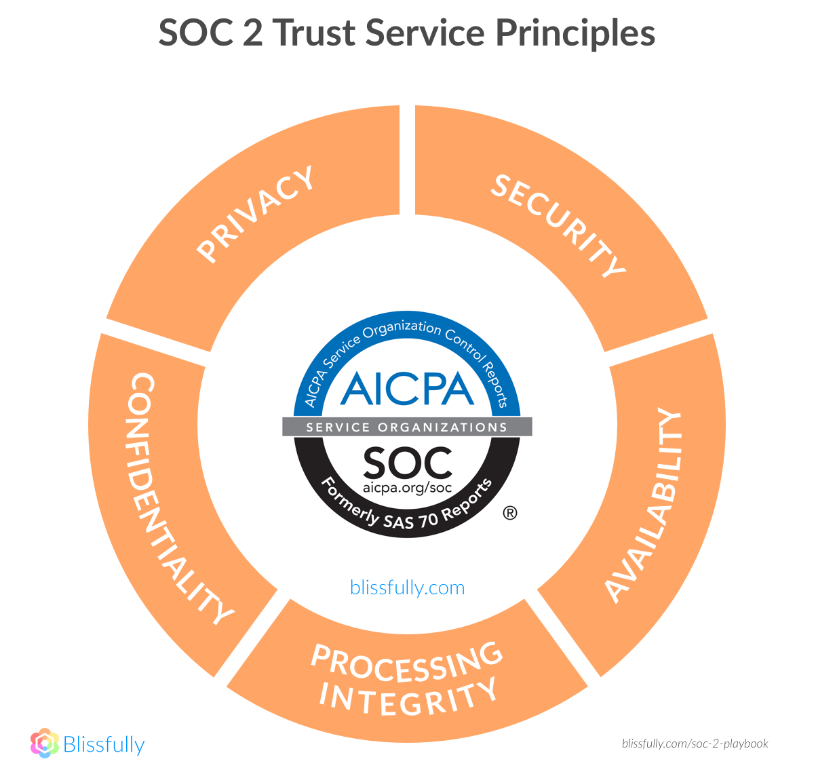
Security. The foundational security principle, common to all audits.
Confidentiality. Protection from unauthorized disclosure of sensitive data.
Availability. Protection that systems or data will be available as agreed or required.
Integrity. Protection that systems or data are not changed in an unauthorized manner.
Privacy. The use, collection, retention, disclosure, and disposal of personal information is protected.
SOC 2 audits are organized around these five "Trust Principles" listed above.
The SOC 2 report is a valuable tool for demonstrating to customers, stakeholders, and regulators that an organization has implemented effective security controls and is committed to protecting sensitive information. The report provides an overview of the organization's controls and procedures, along with the auditor's assessment of their effectiveness.
It is particularly important for service providers that store or process sensitive customer data, such as cloud computing providers, SaaS companies, and data centers. Achieving SOC 2 compliance helps organizations establish trust with customers and demonstrate their commitment to security and data protection.
SOC 2 common criteria
SOC 2 common criteria are the set of requirements that an organization must meet to achieve compliance with the SOC 2 framework.

SOC 2 Timeline
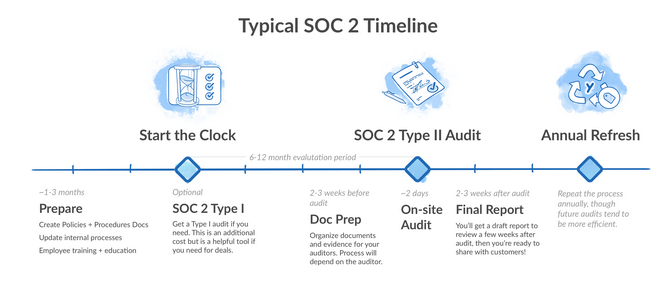
SOC 2 Type I is an audit conducted against the Trust Services Criteria standard at a specific point in time to evaluate the design of the security controls in place. On the other hand, SOC 2 Type II is an audit conducted over a period of time, usually six month or a year, to assess the effectiveness of the security controls. SOC 2 Type II reports are more valuable to customers, prospects, partners, and other stakeholders because they provide a comprehensive evaluation of an organization's security posture over a period of time.
Although SOC 2 Type I reports are quicker to prepare for, it is recommended to work directly toward the Type II report as it emphasizes immediate action taken towards improving security, and there are long-term financial savings as Type II convers Type I.
Why SOC 2 compliance?
SOC 2 compliance is important for companies of all sizes as it helps establish a higher level of trust with customers, prospects, and partners by ensuring that their data is protected. Failure to protect data can result in significant financial losses, brand damage, and reputational harm. The SOC 2 report and Trust Services framework provide external validation that an organization is managing risk appropriately, although there is no guarantee of absolute security.
This validation can help companies retain customers, attract new one, and secure funding.
Four good reasons to pursue SOC 2 compliance
It is important to start SOC 2 preparation early, even if there are no immediate requests for it. This preparation helps improve security by mitigating potential attacks, building a strong security process, and establishing sustainable programs. It also helps bolster company culture by implementing new security controls, providing documentation, and enabling better internal communication and consistency. Finally, preparing for a SOC 2 audit helps with risk management by providing a framework for acknowledging and mitigating risks in a timely manner.
The SOC 2 pyramid
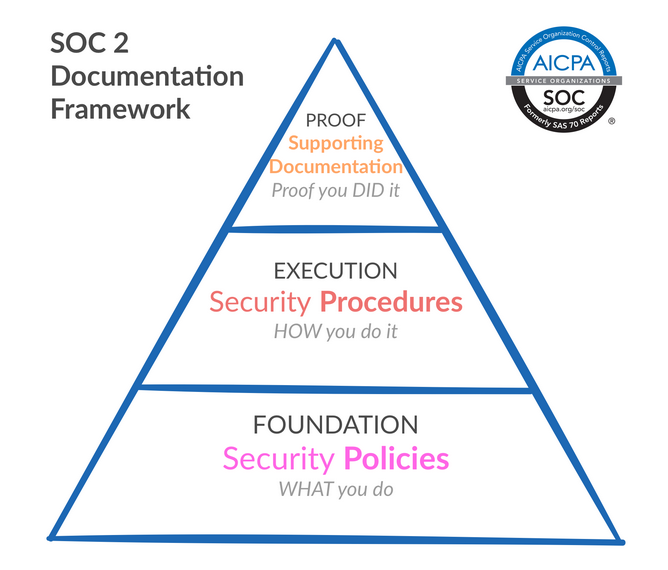
The SOC 2 Pyramid consists of three levels:
- Policies
- Procedures
- Proof
Policies document what the company does to meet security requirements, procedures show how policies are operationalized, and proof provides documentation that demonstrates adherence to policies and procedures.
All SOC 2 examinations require policies related to information security, access control, password, change management, risk assessment and mitigation, incident response, logging and monitoring, vendor management, data classification, acceptable use, information, software and system backup, and business continuity and disaster recovery plan.
Procedures should be meticulously written to describe how the business adheres to policies, and proof requires consistent documentation of day-to-day implementation of key policies.
Questions
1. How would you convince your future company to pursue SOC2 compliance?
In fact, convincing a company to pursue SOC 2 compliance can be approached from several directions. First of all, it is crucial to highlight the benefits or the four good reasons list above of SOC 2 compliance, such as improving overall security, bolstering company culture, providing documentation, and aiding with risk management. These benefits can lead to increased trust from customers and partners, which can result in new business opportunities and improved competitiveness.
Additionally, complying with SOC 2 requirements can prevent costly data breaches and regulatory penalties. It is also important to note that SOC 2 compliance is becoming increasingly important in many industries and may even be required to do business with certain clients. To ensure success, it is recommended to stat SOC 2 preparation early and utilize the SOC 2 Pyramid as a guide.
2. What are the five SOC2 Trust Principles?
The five SOC2 Trust Principles are listed above in What is SOC 2?'s section.
3. How would your explain the three levels of the SOC2 pyramid in an analogy your friends or former colleagues would understand?
The SOC 2 Pyramid can be explained using the analogy of a football game. Policies can be thought of as the plan/preparation for the weekend game, outlining the strenghts and the weaknesses of the other team in order to exploit them. Procedures are like the players doing what it was planned to ensure that everything is done correctly. Finally, proof is like the end of the game, providing evidence that everything it was planned was achieved with success.
Without a solid foundation of policies, the structure of procedures can't be built, and without the structure of procedures, there can be no proof that everything is in compliance.